企业级 Docker 应用:部署、仓库与安全加固
1 Docker简介及部署方法
1.1 Docker简介

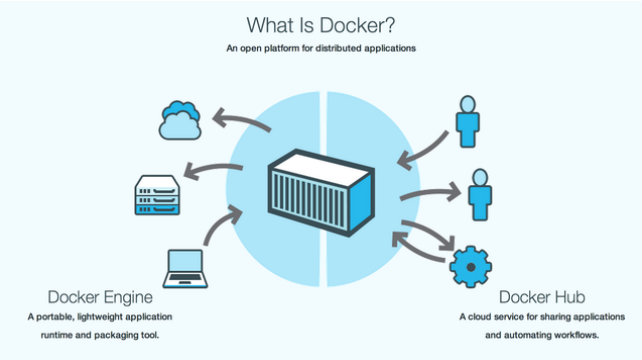
1.1.1 什么是docker?
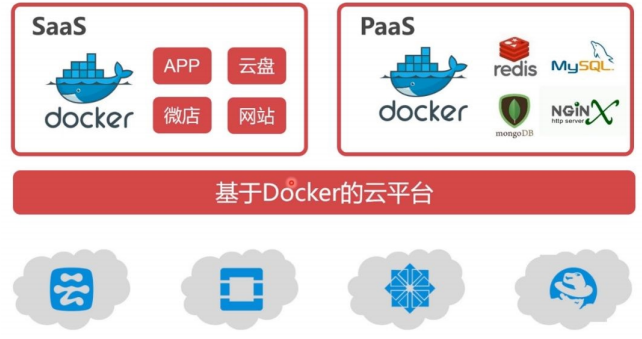
1.1.2 docker在企业中的应用场景
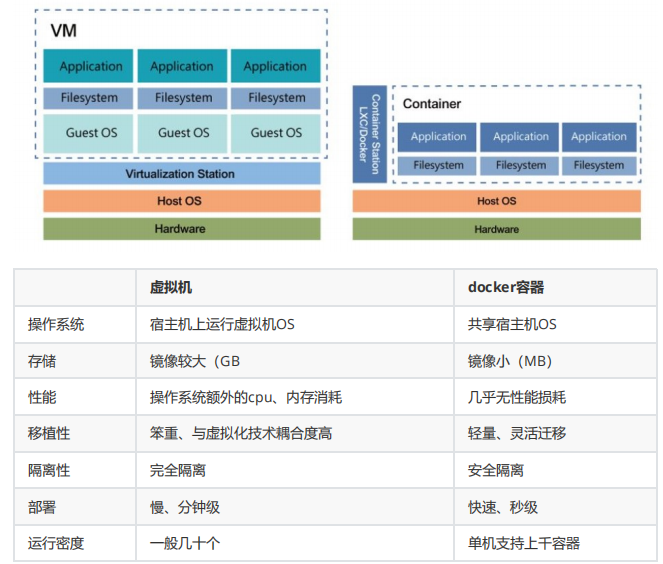
1.1.3 docker与虚拟化的对比
1.1.4 docker的优势
- 对于开发人员:Build once、Run anywhere。
- 对于运维人员:Configure once、Run anything
- 容器技术大大提升了IT人员的幸福指数!
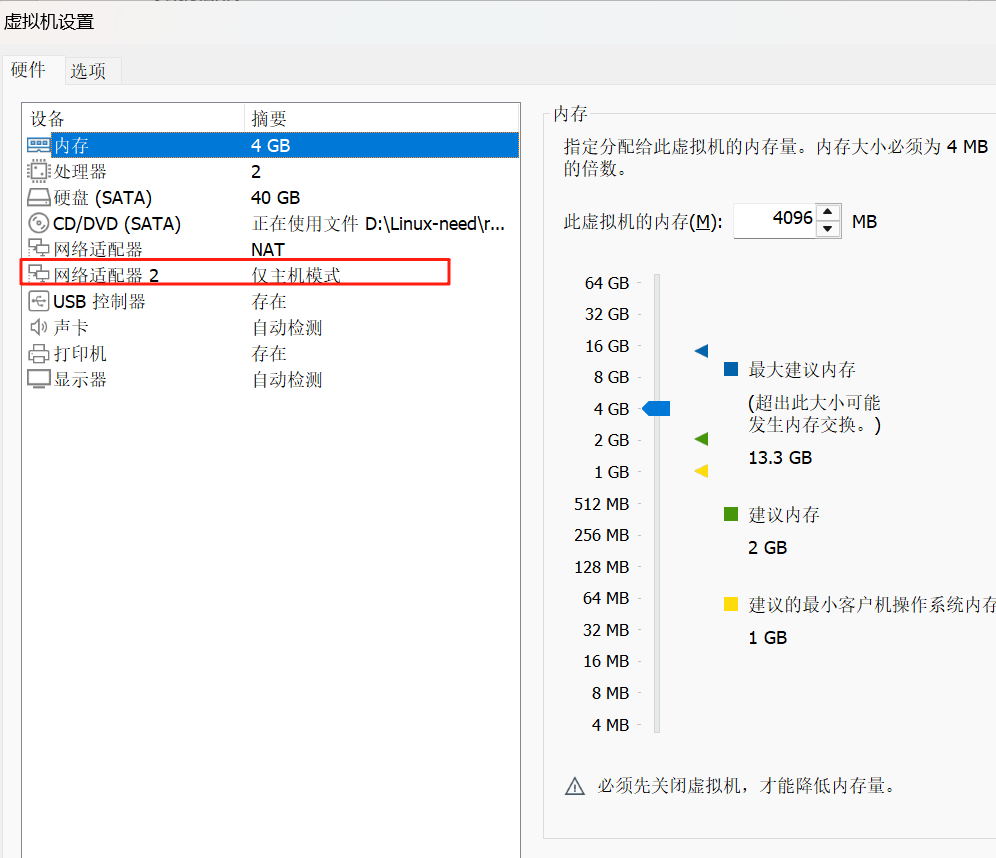
2 部署docker
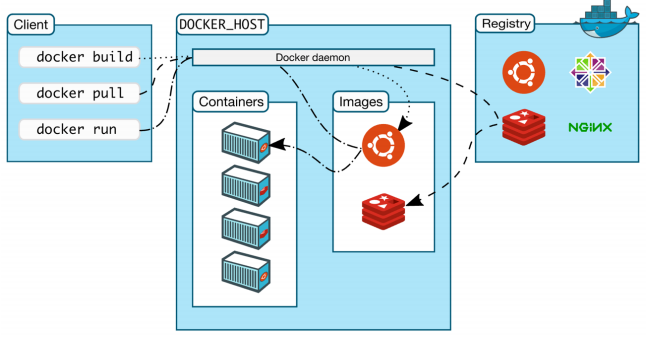
2.1 容器工作方法
2.2 部署第一个容器
2.3 安装docker-ce
2.2.1 配置软件仓库
vim /etc/yum.repos.d/docker.repo编辑如下内容:
[docker]
name=docker-ce
baseurl=https://mirrors.aliyun.com/docker-ce/linux/rhel/9/x86_64/stable
gpgcheck=0卸载podman:
查询podman包
rpm -qa | grep podman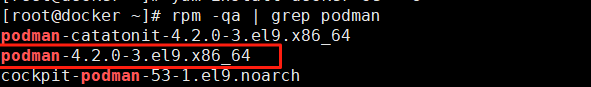
进行卸载:
dnf remove podman-4.2.0-3.el9.x86_64 -y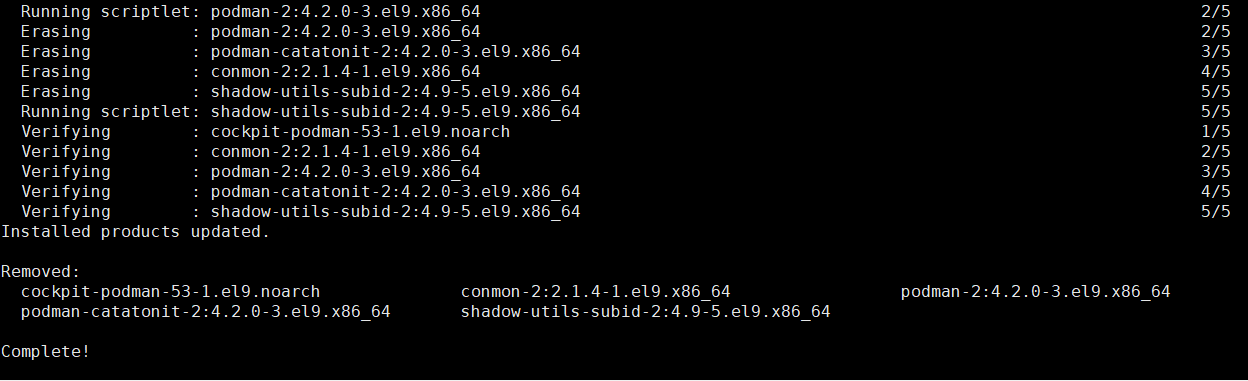
再次查询,确认卸载干净:
rpm -qa | grep podman卸载冲突包:
sudo dnf remove -y buildah runc2.2.2 安装docker-ce并启动服务
yum install -y docker-ce#编辑docker启动文件,设定其使用iptables的网络设定方式,默认使用nftables
vim /lib/systemd/system/docker.service ExecStart=/usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock
--iptables=true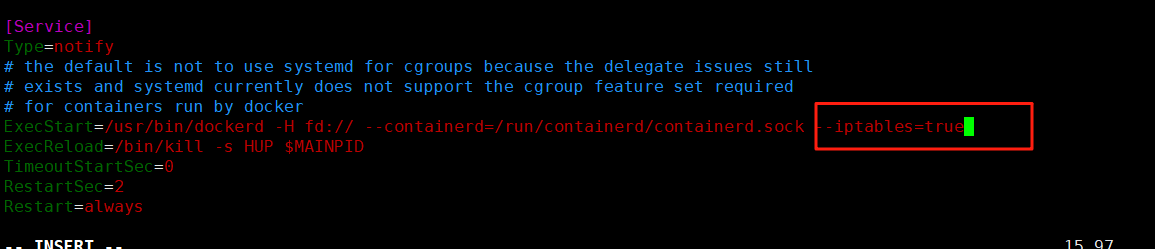
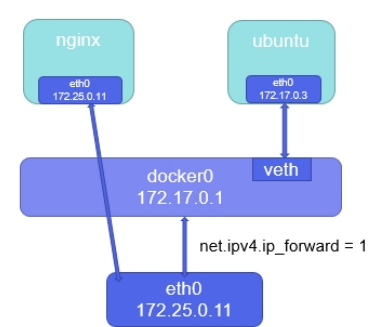
2.2.3 激活内核网络选项
echo net.ipv4.ip_forward = 1 > /etc/sysctl.d/docker.conf刷新系统内核参数和重启 Docker 服务:
sysctl --system
systemctl restart docker(注意)
#在rhel7中 需要
]# vim /etc/sysctl.d/docker.conf
net.bridge.bridge-nf-call-iptables = 1
net.bridge.bridge-nf-call-ip6tables = 1
net.ipv4.ip_forward = 1
]# sysctl --system
]# systemctl restart docker3 Docker的基本操作
3.1 Docker镜像管理:
3.1.1 镜像搜索:
docker search nginx查看本地镜像:
docker images[root@docker packages]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
nginx 1.23 a7be6198544f 2 years ago 142MB3.1.2 拉取镜像:
[root@Docker-node1 ~]# docker pull busybox
[root@Docker-node1 ~]# docker pull nginx:1.26-alpine
3.1.3 查看镜像信息:
docker image inspect nginx:1.23[root@docker packages]# docker image inspect nginx:1.23
[{"Id": "sha256:a7be6198544f09a75b26e6376459b47c5b9972e7aa742af9f356b540fe852cd4","RepoTags": ["nginx:1.23"],"RepoDigests": [],"Parent": "","Comment": "","Created": "2023-05-23T08:51:38.011802405Z","DockerVersion": "20.10.23","Author": "","Architecture": "amd64","Os": "linux","Size": 142145851,"GraphDriver": {"Data": {"LowerDir": "/var/lib/docker/overlay2/e96e76939958426de535ea7d668c10ea0910a2bdafea9776271c0e2d37cf685c/diff:/var/lib/docker/overlay2/b716465abcc0d148b864758dff55bcc4c1ecaa7dab111ea8cedd12986cffdd3c/diff:/var/lib/docker/overlay2/d61e1a60886964ff9f407a0640b16941a0dddb80eb16446a73026364b5eafec9/diff:/var/lib/docker/overlay2/e89fafbf7412f392423c0d014ae9a9d7190ef256420db94746235c442cf466a2/diff:/var/lib/docker/overlay2/1a713b6c5dc96eef002a165325a805bde3b7de0cd00845b43b64b5b8aa90d8cf/diff","MergedDir": "/var/lib/docker/overlay2/181001765be769571578488be650304e134037bb0d4e5364fdd39facc541d91e/merged","UpperDir": "/var/lib/docker/overlay2/181001765be769571578488be650304e134037bb0d4e5364fdd39facc541d91e/diff","WorkDir": "/var/lib/docker/overlay2/181001765be769571578488be650304e134037bb0d4e5364fdd39facc541d91e/work"},"Name": "overlay2"},"RootFS": {"Type": "layers","Layers": ["sha256:8cbe4b54fa88d8fc0198ea0cc3a5432aea41573e6a0ee26eca8c79f9fbfa40e3","sha256:5dd6bfd241b4f4d0bb0a784cd7cefe00829edce2fccb2fcad71244df6344abff","sha256:043198f57be0cb6dd81abe9dd01531faa8dd2879239dc3b798870c0604e1bb3c","sha256:2731b5cfb6163ee5f1fe6126edb946ef11660de5a949404cc76207bf8a9c0e6e","sha256:6791458b394218a2c05b055f952309afa42ec238b74d5165cf1e2ebe9ffe6a33","sha256:4d33db9fdf22934a1c6007dcfbf84184739d590324c998520553d7559a172cfb"]},"Metadata": {"LastTagTime": "0001-01-01T00:00:00Z"},"Config": {"Cmd": ["nginx","-g","daemon off;"],"Entrypoint": ["/docker-entrypoint.sh"],"Env": ["PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin","NGINX_VERSION=1.23.4","NJS_VERSION=0.7.11","PKG_RELEASE=1~bullseye"],"ExposedPorts": {"80/tcp": {}},"Labels": {"maintainer": "NGINX Docker Maintainers \u003cdocker-maint@nginx.com\u003e"},"OnBuild": null,"StopSignal": "SIGQUIT","User": "","Volumes": null,"WorkingDir": ""}}
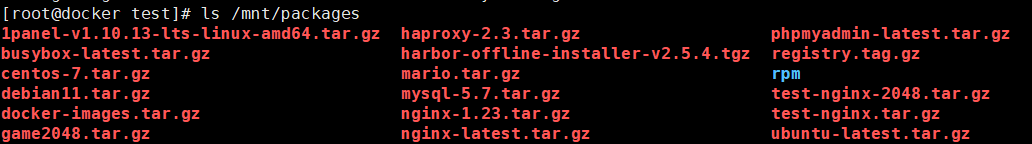
]3.1.4 导入镜像:
docker load -i game2048.tar.gz[root@docker packages]# docker load -i game2048.tar.gz
011b303988d2: Loading layer [==================================================>] 5.05MB/5.05MB
36e9226e74f8: Loading layer [==================================================>] 51.46MB/51.46MB
192e9fad2abc: Loading layer [==================================================>] 3.584kB/3.584kB
6d7504772167: Loading layer [==================================================>] 4.608kB/4.608kB
88fca8ae768a: Loading layer [==================================================>] 629.8kB/629.8kB
Loaded image: timinglee/game2048:latest3.1.5 导出镜像:
镜像保存,
docker image save 名字 : 版本 -o 输出路径
docker image save nginx:1.23 -o test-nginx.tar.gz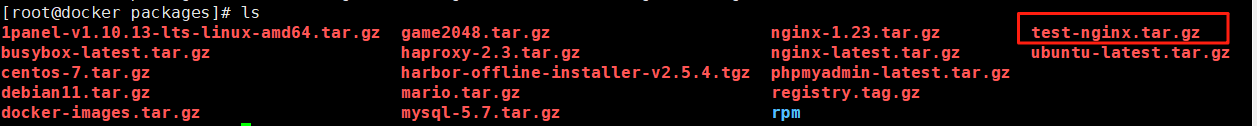
保存导出多个镜像:
docker image save 名字 : 版本 名字 : 版本 -o 输出路径
docker image save nginx:1.23 timinglee/game2048:latest -o test-nginx-2048.tar.gz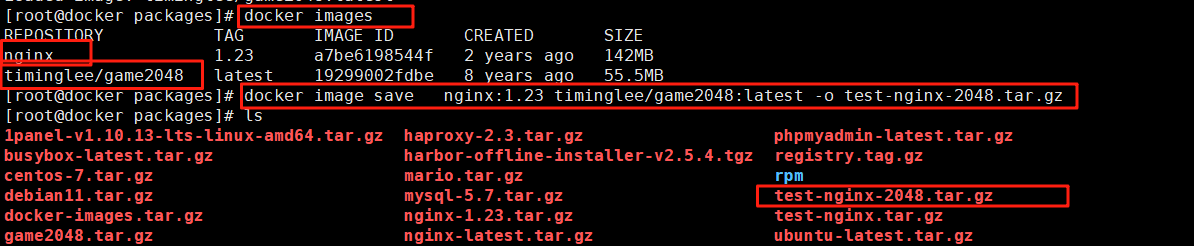
保存所有镜像:
docker save `docker images | awk 'NR>1{print $1":"$2}'` -o images.tar.gz3.1.6 删除镜像:
docker rmi nginx:1.23[root@docker packages]# docker rmi nginx:1.23
Untagged: nginx:1.23
Deleted: sha256:a7be6198544f09a75b26e6376459b47c5b9972e7aa742af9f356b540fe852cd4
Deleted: sha256:b142903ff5d25e779c293678ce1bb71604778bc243cda8c26180675454fbf11c
Deleted: sha256:185fa8597cdc03f83ab9ec3fe21d8ac6fbe49fa65cf8422f05d1d07b06b25fce
Deleted: sha256:1e3de4dfc3a245258917d9cd0860bd30969e1b430ecba95b1eaf2666d8882d24
Deleted: sha256:95b14e2b8329c1fcec4e1df001aac4874bc2247281ae96cdfe355847faf4caa9
Deleted: sha256:8566a5cb57a5d27b0eba5d952429bc542c05853014dc2c8f362540e7533fbff9
Deleted: sha256:8cbe4b54fa88d8fc0198ea0cc3a5432aea41573e6a0ee26eca8c79f9fbfa40e3删除全部镜像:
docker rmi `docker images | awk 'NR>1{print $1":"$2}'`3.2 容器的常用操作
3.2.1 启动容器:
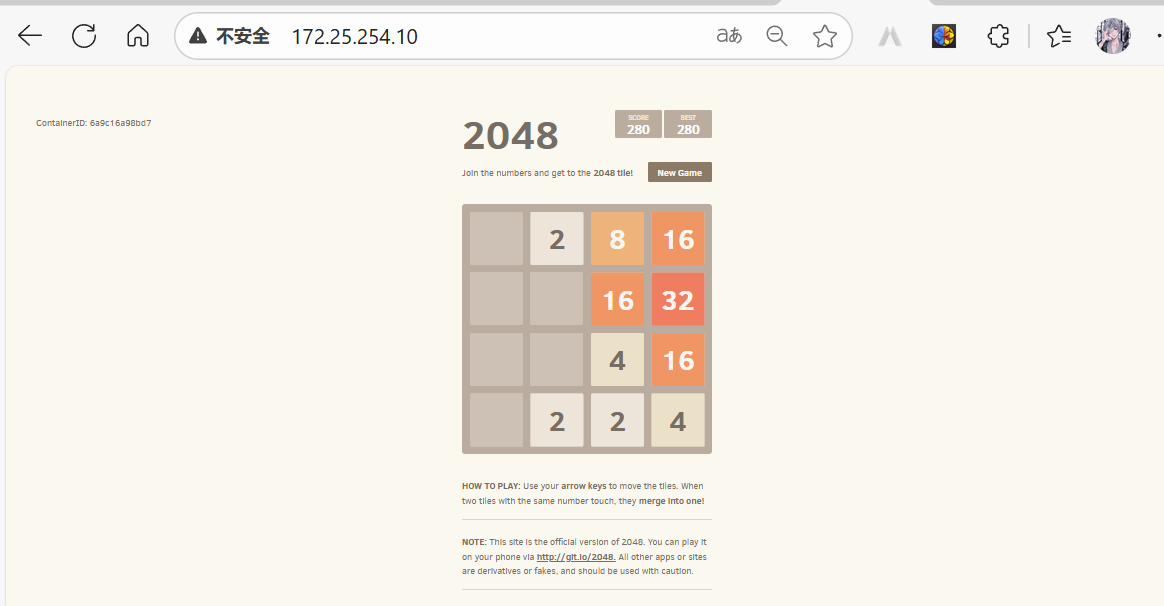
docker run -d --name game2048 -p 80:80 timinglee/game2048查看进程:
docker ps访问容器映射页面:
172.25.254.10:80
-d #后台运行-i #交互式运行-t #打开一个终端--name #指定容器名称-p #端口映射 -p 80:8080 把容器8080端口映射到本机80端口--rm #容器停止自动删除容器--network #指定容器使用的网络
3.2.2 查看容器运行信息
[root@Docker-node1 ~]# docker ps #查看当前运行容器[root@Docker-node1 ~]# docker ps -a #查看所有容器[root@Docker-node1 ~]# docker inspect busybox #查看容器运行的详细信息
3.2.3 停止和运行容器
[root@Docker-node1 ~]# docker stop busybox #停止容器[root@Docker-node1 ~]# docker kill busybox #杀死容器,可以使用信号[root@Docker-node1 ~]# docker start busybox #开启停止的容器
3.2.4 删除容器
[root@Docker-node1 ~]# docker rm centos7 #删除停止的容器[root@Docker-node1 ~]# docker rm -f busybox #删除运行的容器[root@Docker-node1 ~]# docker container prune -f #删除所有停止的容器
[root@Docker-node1 ~]# docker run -it --name test busybox
/ # touch leefile #在容器中建立文件
/ # ls
bin etc leefile lib64 root tmp var
dev home lib proc sys usr
/ #
[root@Docker-node1 ~]# docker rm test #删掉容器后
test
[root@Docker-node1 ~]# docker run -it --name test busybox #删掉容器后开启新的容器文
件不存在
/ # ls
bin dev etc home lib lib64 proc root sys tmp usr var
/ #
[root@Docker-node1 ~]# docker commit -m "add leefile" test busybox:v1
sha256:c8ff62b7480c951635acb6064acdfeb25282bd0c19cbffee0e51f3902cbfa4bd
[root@Docker-node1 ~]# docker images
REPOSITORY TAG IMAGE ID CREATED
SIZE
busybox v1 c8ff62b7480c 12 seconds ago
4.26MB
[root@Docker-node1 ~]# docker image history busybox:v1
IMAGE CREATED CREATED BY SIZE
COMMENT
c8ff62b7480c 2 minutes ago sh 17B add
leefile
65ad0d468eb1 15 months ago BusyBox 1.36.1 (glibc), Debian 12 4.26MB3.2.6 系统中的文件和容器中的文件传输
[root@Docker-node1 ~]# docker cp test2:/leefile /mnt #把容器中的文件复制到本机
Successfully copied 1.54kB to /mnt
[root@Docker-node1 ~]# docker cp /etc/fstab test2:/fstab #把本机文件复制到容器中3.2.7 查询容器内部日志
[root@Docker-node1 ~]# docker logs web
/docker-entrypoint.sh: /docker-entrypoint.d/ is not empty, will attempt to
perform configuration
/docker-entrypoint.sh: Looking for shell scripts in /docker-entrypoint.d/
/docker-entrypoint.sh: Launching /docker-entrypoint.d/10-listen-on-ipv6-bydefault.sh
10-listen-on-ipv6-by-default.sh: info: Getting the checksum of
/etc/nginx/conf.d/default.conf
10-listen-on-ipv6-by-default.sh: info: Enabled listen on IPv6 in
/etc/nginx/conf.d/default.conf
/docker-entrypoint.sh: Sourcing /docker-entrypoint.d/15-local-resolvers.envsh
/docker-entrypoint.sh: Launching /docker-entrypoint.d/20-envsubst-on-templates.sh
/docker-entrypoint.sh: Launching /docker-entrypoint.d/30-tune-worker-processes.sh
/docker-entrypoint.sh: Configuration complete; ready for start up
2024/08/14 07:50:01 [notice] 1#1: using the "epoll" event method
2024/08/14 07:50:01 [notice] 1#1: nginx/1.27.0
2024/08/14 07:50:01 [notice] 1#1: built by gcc 12.2.0 (Debian 12.2.0-14)
2024/08/14 07:50:01 [notice] 1#1: OS: Linux 5.14.0-427.13.1.el9_4.x86_64
2024/08/14 07:50:01 [notice] 1#1: getrlimit(RLIMIT_NOFILE): 1073741816:1073741816
2024/08/14 07:50:01 [notice] 1#1: start worker processes
2024/08/14 07:50:01 [notice] 1#1: start worker process 29
2024/08/14 07:50:01 [notice] 1#1: start worker process 30
172.17.0.1 - - [14/Aug/2024:07:50:20 +0000] "GET / HTTP/1.1" 200 615 "-"
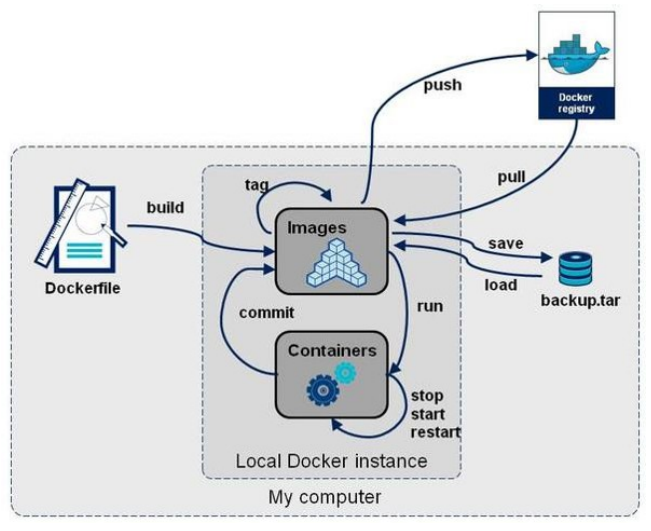
"curl/7.76.1" "-"4 镜像构建
4.1 docker镜像结构
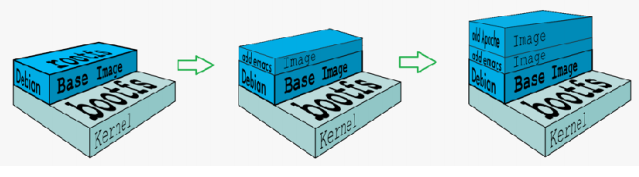
- 共享宿主机的kernel
- base镜像提供的是最小的Linux发行版
- 同一docker主机支持运行多种Linux发行版
- 采用分层结构的最大好处是:共享资源
4.2 镜像运行的基本原理
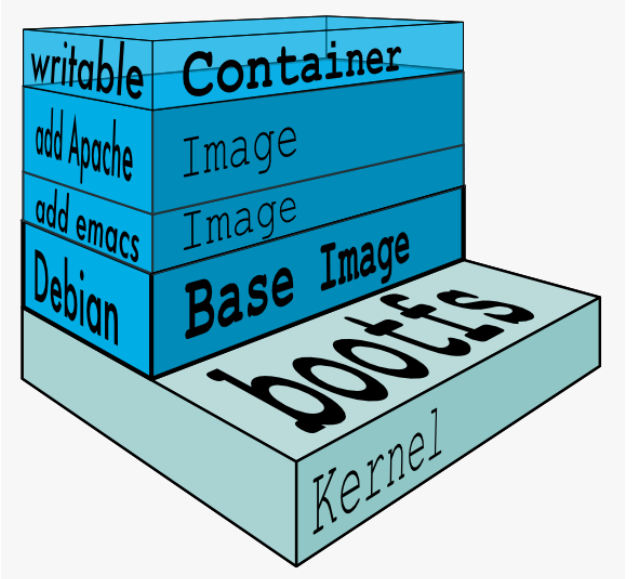
- Copy-on-Write 可写容器层
- 容器层以下所有镜像层都是只读的
- docker从上往下依次查找文件
- 容器层保存镜像变化的部分,并不会对镜像本身进行任何修改
- 一个镜像最多127层
4.3 镜像获得方式
- 基本镜像通常由软件官方提供
- 企业镜像可以用官方镜像+Dockerfile来生成
- 系统关于镜像的获取动作有两种:
- docker pull 镜像地址
- docker load –i 本地镜像包
4.4 镜像构建
4.4.1 构建参数
| FROM | 指定base镜像 eg:FROM busybox:version |
|---|---|
| COPY | 复制文件 eg:COPY file /file 或者 COPY [“file”,”/”] |
| MAINTAINER | 指定作者信息,比如邮箱 eg:MAINTAINER user@example.com 在最新版的docker中用LABEL KEY="VALUE"代替 |
| ADD | 功能和copy相似,指定压缩文件或url eg: ADD test.tar /mnt 或者 eg:ADD http://ip/test.tar /mnt |
| ENV | 指定环境变量 eg:ENV FILENAME test |
| EXPOSE | 暴漏容器端口 eg:EXPOSE 80 |
| VOLUME | 申明数据卷,通常指数据挂载点 eg:VOLUME [“/var/www/html”] |
| WORKDIR | 切换路径 eg:WORKDIR /mnt |
| RUN | 在容器中运行的指令 eg: touch file |
| CMD | 在启动容器时自动运行动作可以被覆盖 eg:CMD echo $FILENAME 会调用shell解析 eg:CMD [“/bin/sh”,”-c”,“echo $FILENAME”] 不调用shell解析 |
| ENTRYPOINT | 和CMD功能和用法类似,但动作不可被覆盖 |
参数示例及用法
FROM COPY 和MAINTAINER
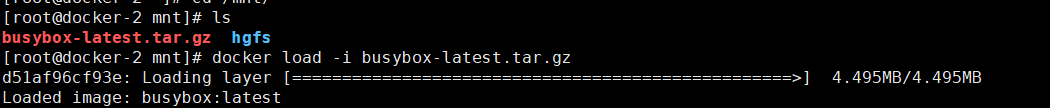
导入要构建的镜像:
docker load -i busybox-latest.tar.gz[root@docker packages]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
busybox latest 65ad0d468eb1 2 years ago 4.26MB
timinglee/game2048 latest 19299002fdbe 8 years ago 55.5MB创建构建文件夹:
mkdir ~/docker
cd ~/docker/编辑构建文件:
touch rin_file
vim rin_fileFROM busybox:latest #指定使用的基础镜像
MAINTAINER rin@rin.com #指定作者信息
COPY rin_file / #复制当前目录文件到容器指定位置,leefile必须在当前目录中构建镜像:
docker build -t example:v1 -f rin_file .查看构建情况:
[root@docker docker]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
example v1 0f34c76c5f1c 9 minutes ago 4.26MB
busybox latest 65ad0d468eb1 2 years ago 4.26MB
timinglee/game2048 latest 19299002fdbe 8 years ago 55.5MB运行容器查看动作是否执行:
docker run -it --rm example:v1 sh[root@docker docker]# docker run -it --rm example:v1 sh
/ # ls
bin etc lib proc root tmp var
dev home lib64 rin_file sys usr
/ # cat rin_file
FROM busybox:latest
MAINTAINER rin@rin.com
COPY rin_file / / # exit4.1.2 镜像构建实例:
当前contos7的软件仓库不可用,重新构建一个软件仓库能用contos7镜像:
将原本的镜像挂载:
docker load -i centos-7.tar.gz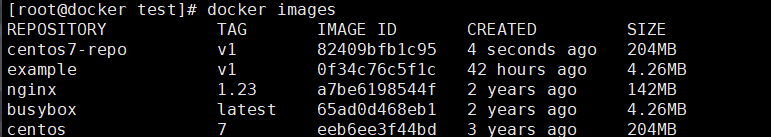
创建构建文件夹,并切换路径:
mkdir /docker/contos7-test
cd /docker/contos7-test编辑要更换的repo文件:
vim rhel7.repo [base]
name = rhel7
baseurl = https://mirrors.aliyun.com/centos/7/os/x86_64/
gpgcheck = 0编辑Dockerfile 文件:
vim Dockerfile
FROM centos:7
RUN rm -f /etc/yum.repos.d/*.repo
COPY rhel7.repo /etc/yum.repos.d/重新构建软件仓库能用的conntos7镜像:
docker build -t centos7-repo:v1 .测试:
进入实例测试,
docker run -it --rm centos7-repo:v1 bash[root@f30a4e3588a0 /]# yum install gcc
Loaded plugins: fastestmirror, ovl
Determining fastest mirrors
base | 3.6 kB 00:00:00
(1/2): base/group_gz | 153 kB 00:00:06
(2/2): base/primary_db | 6.1 MB 00:00:11
Resolving Dependencies
--> Running transaction check
---> Package gcc.x86_64 0:4.8.5-44.el7 will be installed
--> Processing Dependency: libgomp = 4.8.5-44.el7 for package: gcc-4.8.5-44.el7.x86_64
--> Processing Dependency: cpp = 4.8.5-44.el7 for package: gcc-4.8.5-44.el7.x86_64
--> Processing Dependency: glibc-devel >= 2.2.90-12 for package: gcc-4.8.5-44.el7.x86_64
--> Processing Dependency: libmpfr.so.4()(64bit) for package: gcc-4.8.5-44.el7.x86_64
--> Processing Dependency: libmpc.so.3()(64bit) for package: gcc-4.8.5-44.el7.x86_64
--> Processing Dependency: libgomp.so.1()(64bit) for package: gcc-4.8.5-44.el7.x86_64
--> Running transaction check
---> Package cpp.x86_64 0:4.8.5-44.el7 will be installed
---> Package glibc-devel.x86_64 0:2.17-317.el7 will be installed
--> Processing Dependency: glibc-headers = 2.17-317.el7 for package: glibc-devel-2.17-317.el7.x86_64
--> Processing Dependency: glibc-headers for package: glibc-devel-2.17-317.el7.x86_64
---> Package libgomp.x86_64 0:4.8.5-44.el7 will be installed
---> Package libmpc.x86_64 0:1.0.1-3.el7 will be installed
---> Package mpfr.x86_64 0:3.1.1-4.el7 will be installed
--> Running transaction check
---> Package glibc-headers.x86_64 0:2.17-317.el7 will be installed
--> Processing Dependency: kernel-headers >= 2.2.1 for package: glibc-headers-2.17-317.el7.x86_64
--> Processing Dependency: kernel-headers for package: glibc-headers-2.17-317.el7.x86_64
--> Running transaction check
---> Package kernel-headers.x86_64 0:3.10.0-1160.el7 will be installed
--> Finished Dependency ResolutionDependencies Resolved============================================================================================================================Package Arch Version Repository Size
============================================================================================================================
Installing:gcc x86_64 4.8.5-44.el7 base 16 M
Installing for dependencies:cpp x86_64 4.8.5-44.el7 base 5.9 Mglibc-devel x86_64 2.17-317.el7 base 1.1 Mglibc-headers x86_64 2.17-317.el7 base 690 kkernel-headers x86_64 3.10.0-1160.el7 base 9.0 Mlibgomp x86_64 4.8.5-44.el7 base 159 klibmpc x86_64 1.0.1-3.el7 base 51 kmpfr x86_64 3.1.1-4.el7 base 203 kTransaction Summary
============================================================================================================================
Install 1 Package (+7 Dependent packages)Total download size: 33 M
Installed size: 60 M
Is this ok [y/d/N]: n
4.5 镜像优化:
- 选择最精简的基础镜像
- 减少镜像的层数
- 清理镜像构建的中间产物
- 选择最精简的基础镜像
- 减少镜像的层数
- 清理镜像构建的中间产物
4.5.2 镜像优化示例
[root@server1 docker]# vim Dockerfile
FROM centos:7 as build
ADD nginx-1.23.3.tar.gz /mnt
WORKDIR /mnt/nginx-1.23.3
RUN yum install -y gcc make pcre-devel openssl-devel && sed -i 's/CFLAGS="$CFLAGS
-g"/#CFLAGS="$CFLAGS -g"/g' auto/cc/gcc && ./configure --with-http_ssl_module --
with-http_stub_status_module && make && make install && cd .. && rm -fr nginx-
1.23.3 && yum clean all
EXPOSE 80
VOLUME ["/usr/local/nginx/html"]
CMD ["/usr/local/nginx/sbin/nginx", "-g", "daemon off;"]
[root@server1 docker]# docker build -t webserver:v2 .
[root@server1 docker]# docker images webserver
REPOSITORY TAG IMAGE ID CREATED SIZE
webserver v2 caf0f80f2332 4 seconds ago 317MB
webserver v1 bfd6774cc216 About an hour ago 494MB[root@server1 docker]# vim Dockerfile
FROM centos:7 as build
ADD nginx-1.23.3.tar.gz /mnt
WORKDIR /mnt/nginx-1.23.3
RUN yum install -y gcc make pcre-devel openssl-devel && sed -i 's/CFLAGS="$CFLAGS
-g"/#CFLAGS="$CFLAGS -g"/g' auto/cc/gcc && ./configure --with-http_ssl_module --
with-http_stub_status_module && make && make install && cd .. && rm -fr nginx-
1.23.3 && yum clean all
FROM centos:7
COPY --from=build /usr/local/nginx /usr/local/nginx
EXPOSE 80
VOLUME ["/usr/local/nginx/html"]
CMD ["/usr/local/nginx/sbin/nginx", "-g", "daemon off;"]
[root@server1 docker]# docker build -t webserver:v3 .
[root@server1 docker]# docker images webserver
REPOSITORY TAG IMAGE ID CREATED SIZE
webserver v3 1ac964f2cefe 29 seconds ago 205MB
webserver v2 caf0f80f2332 3 minutes ago 317MB
webserver v1 bfd6774cc216 About an hour ago 494MBdocker pull gcr.io/distroless/base[root@server1 ~]# mkdir new
[root@server1 ~]# cd new/
[root@server1 new]# vim Dockerfile
FROM nginx:latest as base
# https://en.wikipedia.org/wiki/List_of_tz_database_time_zones
ARG TIME_ZONE
RUN mkdir -p /opt/var/cache/nginx && \
cp -a --parents /usr/lib/nginx /opt && \
cp -a --parents /usr/share/nginx /opt && \
cp -a --parents /var/log/nginx /opt && \
cp -aL --parents /var/run /opt && \
cp -a --parents /etc/nginx /opt && \
cp -a --parents /etc/passwd /opt && \
cp -a --parents /etc/group /opt && \
cp -a --parents /usr/sbin/nginx /opt && \
cp -a --parents /usr/sbin/nginx-debug /opt && \
cp -a --parents /lib/x86_64-linux-gnu/ld-* /opt && \
cp -a --parents /usr/lib/x86_64-linux-gnu/libpcre* /opt && \
cp -a --parents /lib/x86_64-linux-gnu/libz.so.* /opt && \
cp -a --parents /lib/x86_64-linux-gnu/libc* /opt && \
cp -a --parents /lib/x86_64-linux-gnu/libdl* /opt && \
cp -a --parents /lib/x86_64-linux-gnu/libpthread* /opt && \
cp -a --parents /lib/x86_64-linux-gnu/libcrypt* /opt && \
cp -a --parents /usr/lib/x86_64-linux-gnu/libssl.so.* /opt && \
cp -a --parents /usr/lib/x86_64-linux-gnu/libcrypto.so.* /opt && \
cp /usr/share/zoneinfo/${TIME_ZONE:-ROC} /opt/etc/localtime
FROM gcr.io/distroless/base-debian11
COPY --from=base /opt /
EXPOSE 80 443
ENTRYPOINT ["nginx", "-g", "daemon off;"]
[root@server1 new]# docker build -t webserver:v4 .
[root@server1 new]# docker images webserver
REPOSITORY TAG IMAGE ID CREATED SIZE
webserver v4 c0c4e1d49f3d 4 seconds ago 34MB
webserver v3 1ac964f2cefe 12 minutes ago 205MB
webserver v2 caf0f80f2332 15 minutes ago 317MB
webserver v1 bfd6774cc216 About an hour ago 494MB5 Docker 镜像仓库的管理
5.1什么是docker仓库
- 公共仓库,如 Docker Hub,任何人都可以访问和使用其中的镜像。许多常用的软件和应用都有在
- Docker Hub 上提供的镜像,方便用户直接获取和使用。
- 例如,您想要部署一个 Nginx 服务器,就可以从 Docker Hub 上拉取 Nginx 的镜像。
- 私有仓库则是由组织或个人自己搭建和管理的,用于存储内部使用的、不希望公开的镜像。
- 比如,一家企业为其特定的业务应用创建了定制化的镜像,并将其存储在自己的私有仓库中, 以保证安全性和控制访问权限。
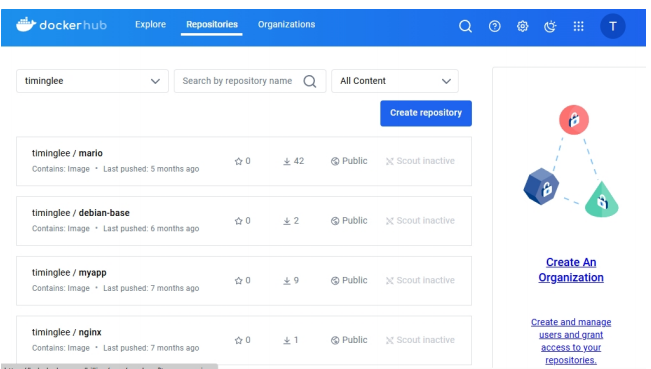
5.2 docker hub
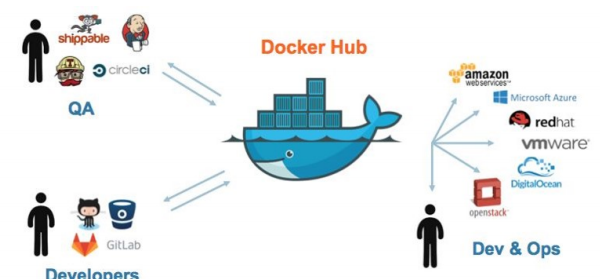
- 例如,您可以轻松找到 Ubuntu、CentOS 等操作系统的镜像,以及 MySQL、Redis 等数据库 的镜像。
5.2.1 docker hub的使用方法
#登陆官方仓库
[root@docker ~]# docker login
Log in with your Docker ID or email address to push and pull images from Docker
Hub. If you don't have a Docker ID, head over to https://hub.docker.com/ to
create one.
You can log in with your password or a Personal Access Token (PAT). Using a
limited-scope PAT grants better security and is required for organizations using
SSO. Learn more at https://docs.docker.com/go/access-tokens/
Username: timinglee
Password:
WARNING! Your password will be stored unencrypted in /root/.docker/config.json.
Configure a credential helper to remove this warning. See
https://docs.docker.com/engine/reference/commandline/login/#credential-stores
Login Succeeded
#登陆信息保存位置
[root@docker ~]# cd .docker/
[root@docker .docker]# ls
config.json
[root@docker .docker]# cat config.json
{
"auths": {
"https://index.docker.io/v1/": {
"auth": "dGltaW5nbGVlOjY3NTE1MTVtaW5nemxu"
}
}
[root@docker ~]# docker tag gcr.io/distroless/base-debian11:latest
timinglee/base-debian11:latest
[root@docker ~]# docker push timinglee/base-debian11:latest
The push refers to repository [docker.io/timinglee/base-debian11]
6835249f577a: Pushed
24aacbf97031: Pushed
8451c71f8c1e: Pushed
2388d21e8e2b: Pushed
c048279a7d9f: Pushed
1a73b54f556b: Pushed
2a92d6ac9e4f: Pushed
bbb6cacb8c82: Pushed
ac805962e479: Pushed
af5aa97ebe6c: Pushed
4d049f83d9cf: Pushed
9ed498e122b2: Pushed
577c8ee06f39: Pushed
5342a2647e87: Pushed
latest: digest:
sha256:f8179c20f1f2b1168665003412197549bd4faab5ccc1b140c666f9b8aa958042 size:
3234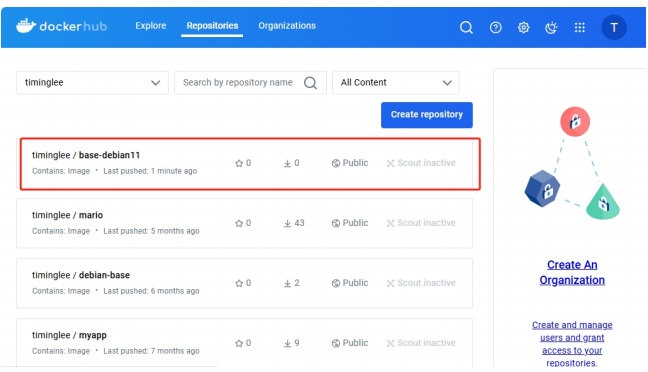
5.3 docker仓库的工作原理
5.3.1pull原理
- 镜像拉取分为以下几步:
- docker客户端向index发送镜像拉去请求并完成与index的认证
- index发送认证token和镜像位置给dockerclient
- dockerclient携带token和根据index指引的镜像位置取连接registry
- Registry会根据client持有的token跟index核实身份合法性
- index确认此token合法性
- Registry会根据client的请求传递镜像到客户端
5.3.2 push原理
- client向index发送上传请求并完成用户认证
- index会发方token给client来证明client的合法性
- client携带index提供的token连接Registry
- Registry向index合适token的合法性
- index证实token的合法性
- Registry开始接收客户端上传过来的镜像
5.4 搭建docker的私有仓库
5.4.1 为什么搭建私有仓库
- 需要internet连接,速度慢
- 所有人都可以访问
- 由于安全原因企业不允许将镜像放到外网
5.4.2 搭建简单的Registry仓库
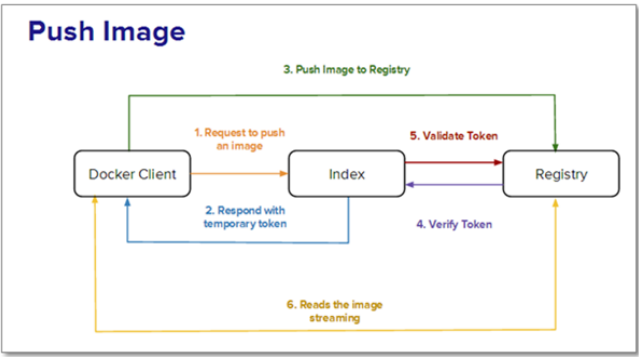
docker load -i registry.tag.gz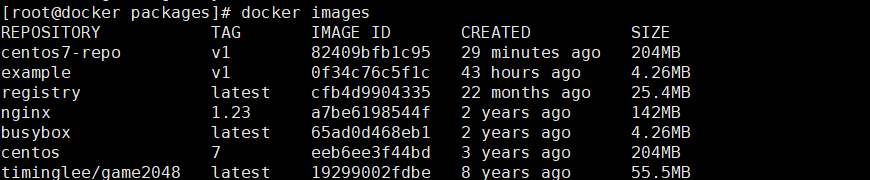
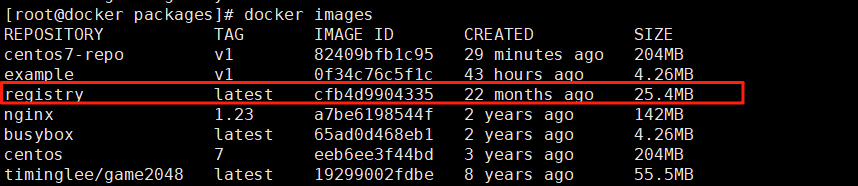
docker run -d -p 5000:5000 --restart=always --name registry registry:latest查看进程:
[root@docker packages]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
3cb75b901caa registry:latest "/entrypoint.sh /etc…" 39 seconds ago Up 38 seconds 0.0.0.0:5000->5000/tcp, [::]:5000->5000/tcp registry5.4.3上传镜像到仓库:
5.4.3.1免密上传:
vim /etc/docker/daemon.json{
"insecure-registries" : ["http://172.25.254.10:5000"]
}重启docker:
systemctl restart docker上传镜像:
给要传的镜像打标签:
docker tag busybox:latest 172.25.254.10:5000/busybox:latest上传:
docker push 172.25.254.10:5000/busybox:latest查看上传好的镜像:
[root@docker packages]# curl 172.25.254.10:5000/v2/_catalog
{"repositories":["busybox"]}测试:
将镜像目录的busybox删除:
docker rmi busybox:latest[root@docker packages]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
centos7-repo v1 82409bfb1c95 43 minutes ago 204MB
example v1 0f34c76c5f1c 43 hours ago 4.26MB
registry latest cfb4d9904335 22 months ago 25.4MB
nginx 1.23 a7be6198544f 2 years ago 142MB
172.25.254.100:5000/busybox latest 65ad0d468eb1 2 years ago 4.26MB
172.25.254.10:5000/busybox latest 65ad0d468eb1 2 years ago 4.26MB
centos 7 eeb6ee3f44bd 3 years ago 204MB
timinglee/game2048 latest 19299002fdbe 8 years ago 55.5MB再从本地仓库拉取:
docker pull 172.25.254.10:5000/busybox:latest[root@docker packages]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
centos7-repo v1 82409bfb1c95 46 minutes ago 204MB
example v1 0f34c76c5f1c 43 hours ago 4.26MB
registry latest cfb4d9904335 22 months ago 25.4MB
nginx 1.23 a7be6198544f 2 years ago 142MB
172.25.254.10:5000/busybox latest 65ad0d468eb1 2 years ago 4.26MB
centos 7 eeb6ee3f44bd 3 years ago 204MB
timinglee/game2048 latest 19299002fdbe 8 years ago 55.5MB5.4.3.2 加密传输:
创建证书存放文件夹:
mkdir -p /root/certs
cd /rootopenssl req -newkey rsa:4096 \
-nodes -sha256 -keyout certs/rin.key \
-addext "subjectAltName = DNS:www.rin.com" \
-x509 -days 365 -out certs/rin.crtCountry Name (2 letter code) [XX]:CN
State or Province Name (full name) []:guangxi
Locality Name (eg, city) [Default City]:nanning
Organization Name (eg, company) [Default Company Ltd]:rin
Organizational Unit Name (eg, section) []:docker
Common Name (eg, your name or your server's hostname) []:www.rin.com #其余随意填,这条得填跟上面dns一样的内容
Email Address []:rin@rin.com
docker run -d -p 443:443 --restart=always --name registry \
--name registry -v /opt/registry:/var/lib/registry \
-v /root/certs:/certs \
-e REGISTRY_HTTP_ADDR=0.0.0.0:443 \
-e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/rin.crt \
-e REGISTRY_HTTP_TLS_KEY=/certs/rin.key registry
将证书复制到 Docker 的证书信任目录中
# 1. 创建证书目录(注意替换为你的域名 www.rin.com)
sudo mkdir -p /etc/docker/certs.d/www.rin.com # 2. 将证书复制到该目录(假设证书在当前主机的 /root/certs/rin.crt)
cp /root/certs/rin.crt /etc/docker/certs.d/www.rin.com/ca.crt # 3. 重启 Docker 服务使配置生效
sudo systemctl restart docker# 为busybox镜像添加标签,并推送:
# 为busybox镜像添加标签(假设你要推送的是busybox这个镜像)
docker tag busybox:latest www.rin.com/busybox:latest # 进行推送了
docker push www.rin.com/busybox:latest查看推送情况:
[root@docker ~]# curl -k https://www.rin.com/v2/_catalog
{"repositories":["busybox"]}5.4.4 为仓库建立登陆认证
dnf install httpd-tools -ymkdir auth#-B 强制使用最安全加密方式,默认用md5加密
htpasswd -Bc auth/htpasswd rin[root@docker ~]# htpasswd -Bc /root/auth/htpasswd rin
New password:
Re-type new password:
Adding password for user rin docker run -d -p 443:443
--restart=always
--name registry
-v /opt/registry:/var/lib/registry
-v /root/certs:/certs
-e REGISTRY_HTTP_ADDR=0.0.0.0:443
-e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/rin.crt
-e REGISTRY_HTTP_TLS_KEY=/certs/rin.key
-v /root/auth:/auth
-e "REGISTRY_AUTH=htpasswd"
-e "REGISTRY_AUTH_HTPASSWD_REALM=Registry Realm"
-e REGISTRY_AUTH_HTPASSWD_PATH=/auth/htpasswd registry
测试:
[root@docker ~]# curl -k https://www.rin.com/v2/_catalog -u rin:123
{"repositories":["busybox"]}登入测试:
docker login www.rin.com[root@docker ~]# docker login www.rin.com
Username: rin
Password: WARNING! Your credentials are stored unencrypted in '/root/.docker/config.json'.
Configure a credential helper to remove this warning. See
https://docs.docker.com/go/credential-store/Login Succeeded5.5 构建企业级私有仓库

- 基于角色的访问控制(RBAC):可以为不同的用户和用户组分配不同的权限,增强了安全性和管理的灵活性。
- 镜像复制:支持在不同的 Harbor 实例之间复制镜像,方便在多个数据中心或环境中分发镜像。
- 图形化用户界面(UI):提供了直观的 Web 界面,便于管理镜像仓库、项目、用户等。
- 审计日志:记录了对镜像仓库的各种操作,有助于追踪和审查活动。
- 垃圾回收:可以清理不再使用的镜像,节省存储空间。
5.5.1 部署harbor
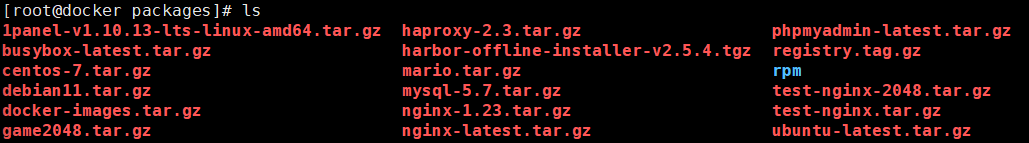
tar xzf harbor-offline-installer-v2.5.4.tgz创建证书存放文件夹:
mkdir -p /data/certs
cd /dataopenssl req -newkey rsa:4096 \
-nodes -sha256 -keyout certs/rin.key \
-addext "subjectAltName = DNS:www.rin.com" \
-x509 -days 365 -out certs/rin.crtCountry Name (2 letter code) [XX]:CN
State or Province Name (full name) []:guangxi
Locality Name (eg, city) [Default City]:nanning
Organization Name (eg, company) [Default Company Ltd]:rin
Organizational Unit Name (eg, section) []:docker
Common Name (eg, your name or your server's hostname) []:www.rin.com #其余随意填,这条得填跟上面dns一样的内容
Email Address []:rin@rin.com
编辑文件:
cd harbor/
cp harbor.yml.tmpl harbor.yml
vim harbor.yml# Configuration file of Harbor# The IP address or hostname to access admin UI and registry service.
# DO NOT use localhost or 127.0.0.1, because Harbor needs to be accessed by external clients.
hostname: www.rin.com# https related config
https:# https port for harbor, default is 443port: 443# The path of cert and key files for nginxcertificate: /data/certs/rin.crtprivate_key: /data/certs/rin.key# The initial password of Harbor admin
# It only works in first time to install harbor
# Remember Change the admin password from UI after launching Harbor.
harbor_admin_password: rin# The default data volume
data_volume: /data执行安装脚本:
执行前记得将同名镜像容器删除:
docker rm -f registry./install.sh --with-chartmuseumdocker compose stop
docker compose up -d[root@docker harbor]# docker compose stop
WARN[0000] /mnt/packages/harbor/docker-compose.yml: the attribute `version` is obsolete, it will be ignored, please remove it to avoid potential confusion
[+] Stopping 10/10✔ Container harbor-jobservice Stopped 0.6s ✔ Container registryctl Stopped 10.2s ✔ Container chartmuseum Stopped 0.6s ✔ Container nginx Stopped 0.5s ✔ Container harbor-portal Stopped 0.3s ✔ Container harbor-core Stopped 3.3s ✔ Container registry Stopped 0.2s ✔ Container redis Stopped 0.5s ✔ Container harbor-db Stopped 0.3s ✔ Container harbor-log Stopped 10.3s
[root@docker harbor]# docker compose up -d
WARN[0000] /mnt/packages/harbor/docker-compose.yml: the attribute `version` is obsolete, it will be ignored, please remove it to avoid potential confusion
[+] Running 10/10✔ Container harbor-log Started 0.5s ✔ Container harbor-portal Started 2.6s ✔ Container harbor-db Started 1.1s ✔ Container redis Started 2.8s ✔ Container registry Started 2.8s ✔ Container chartmuseum Started 2.7s ✔ Container registryctl Started 2.7s ✔ Container harbor-core Started 1.0s ✔ Container nginx Started 1.3s ✔ Container harbor-jobservice Started 0.7s 5.5.2 管理仓库
登录私有仓库:
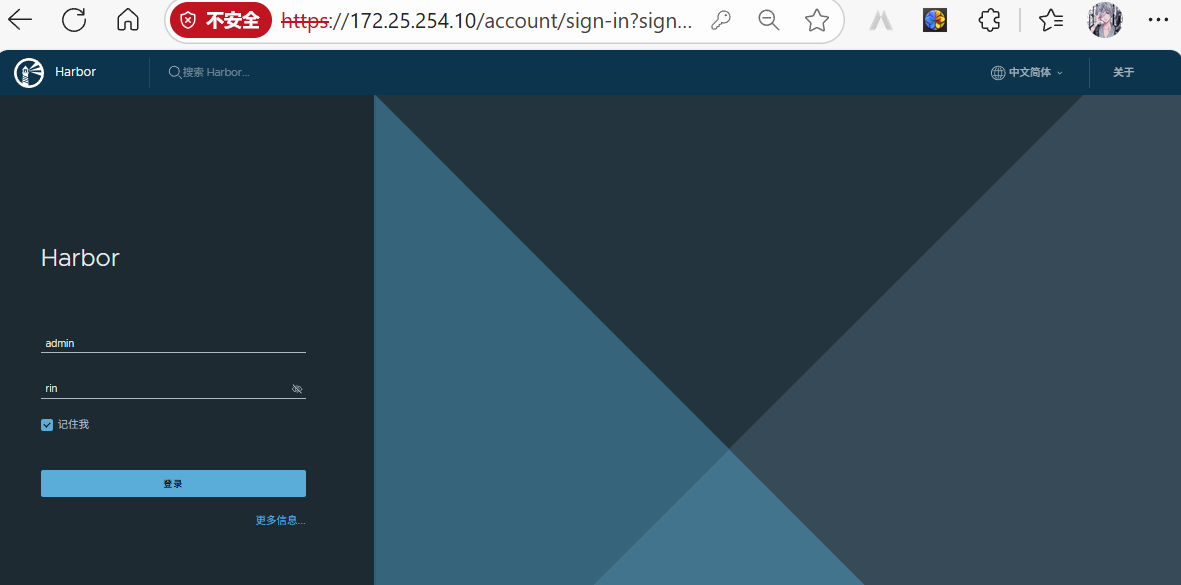
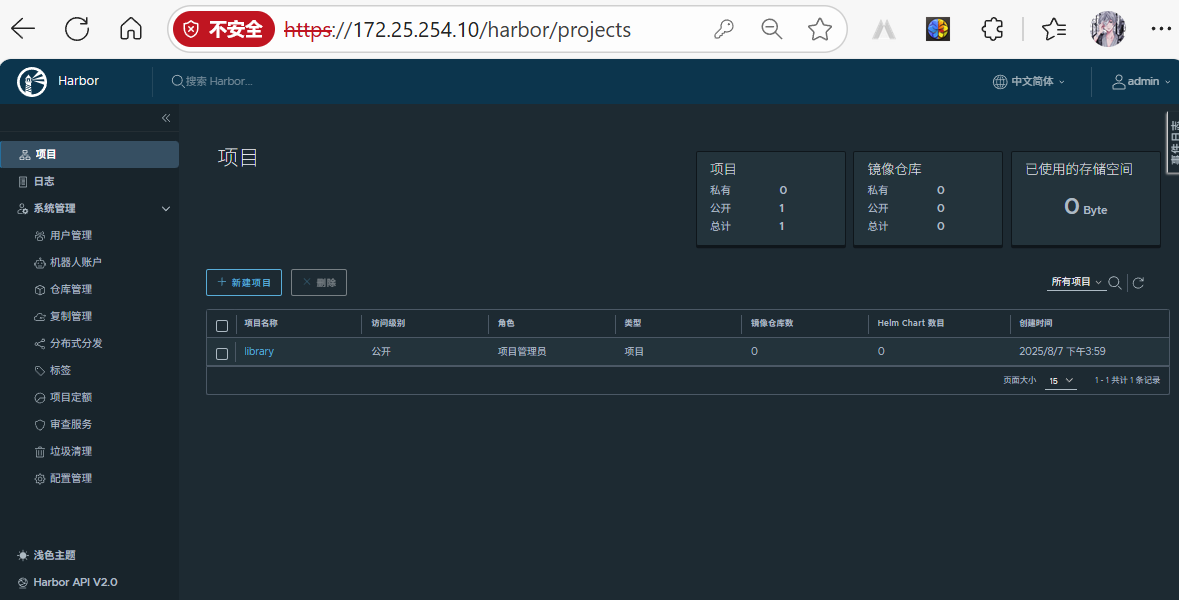
建立仓库项目:
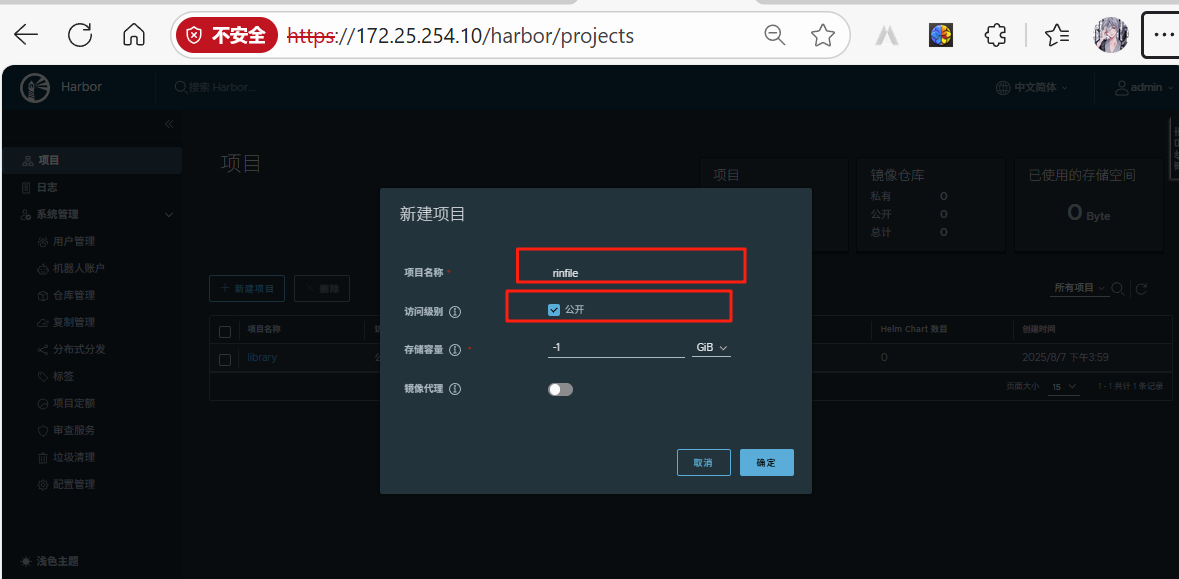
上传镜像:
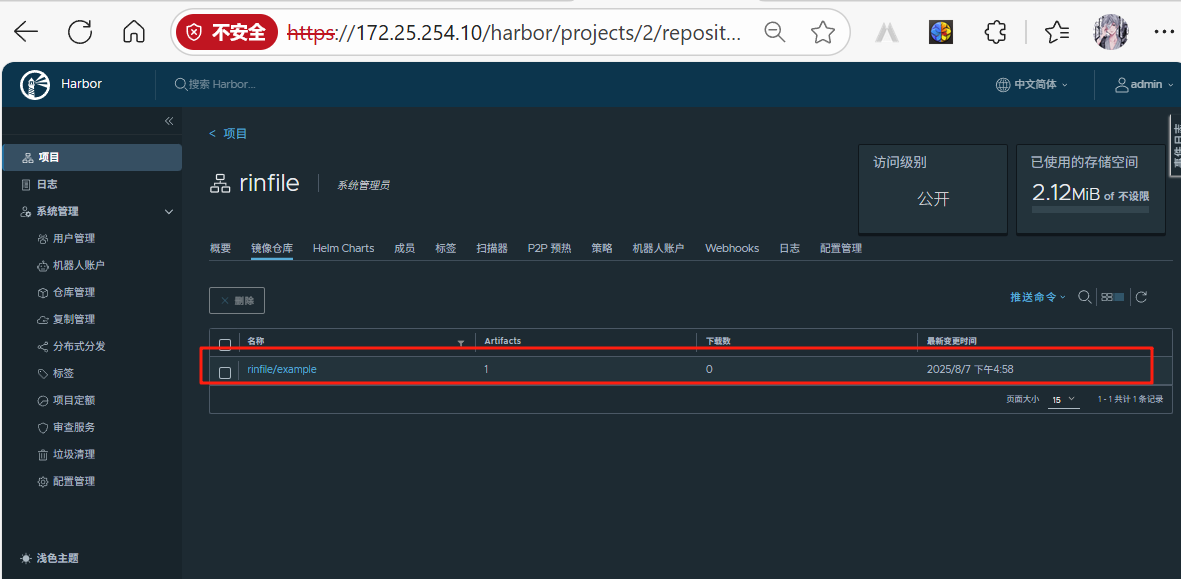
[root@docker harbor]# docker push www.rin.com/rinfile/example:v1
The push refers to repository [www.rin.com/rinfile/example]
bcbeb1265327: Pushed
d51af96cf93e: Pushed
v1: digest: sha256:64743a2cdb84b0a21e7132de9bdc8d592cc3b90a035b93c05cf6941620b43d27 size: 734
添加标签:
docker tag 本地镜像 仓库地址/项目名/镜像名:标签
docker tag example:v1 www.rin.com/rinfile/example:v1上传镜像:
docker push www.rin.com/rinfile/example:v1[root@docker harbor]# docker push www.rin.com/rinfile/example:v1
The push refers to repository [www.rin.com/rinfile/example]
bcbeb1265327: Pushed
d51af96cf93e: Pushed
v1: digest: sha256:64743a2cdb84b0a21e7132de9bdc8d592cc3b90a035b93c05cf6941620b43d27 size: 734查看上传的镜像:
6 Docker 网络
[root@docker harbor]# docker network lsNETWORK ID NAME DRIVER SCOPE2a93d6859680 bridge bridge local4d81ddd9ed10 host host local8c8c95f16b68 none null local
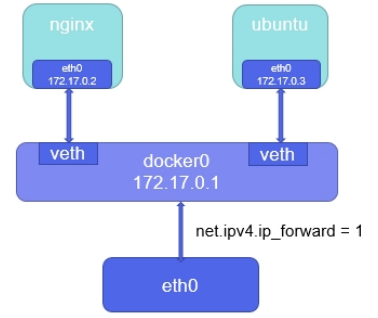
6.1 docker原生bridge网路
[root@docker mnt]# ip link show type bridge
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN
mode DEFAULT group default
link/ether 02:42:5f:e2:34:6c brd ff:ff:ff:ff:ff:ff- bridge模式下容器没有一个公有ip,只有宿主机可以直接访问,外部主机是不可见的。
- 容器通过宿主机的NAT规则后可以访问外网
[root@docker mnt]# docker run -d --name web -p 80:80 nginx:1.23
defeba839af1b95bac2a200fd1e06a45e55416be19c7e9ce7e0c8daafa7dd470
[root@docker mnt]# ifconfig
docker0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.17.0.1 netmask 255.255.0.0 broadcast 172.17.255.255
inet6 fe80::42:5fff:fee2:346c prefixlen 64 scopeid 0x20<link>
ether 02:42:5f:e2:34:6c txqueuelen 0 (Ethernet)
RX packets 21264 bytes 1497364 (1.4 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 27358 bytes 215202237 (205.2 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.25.254.100 netmask 255.255.255.0 broadcast 172.25.254.255
inet6 fe80::30b2:327e:b13a:31cf prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ec:fc:d3 txqueuelen 1000 (Ethernet)
RX packets 1867778 bytes 2163432019 (2.0 GiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 822980 bytes 848551940 (809.2 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 11819 bytes 1279944 (1.2 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 11819 bytes 1279944 (1.2 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
veth022a7c9: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet6 fe80::a013:5fff:fefc:c9e4 prefixlen 64 scopeid 0x20<link>
ether a2:13:5f:fc:c9:e4 txqueuelen 0 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 15 bytes 2007 (1.9 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0[root@docker mnt]# brctl show
bridge name bridge id STP enabled interfaces
docker0 8000.02425fe2346c no veth022a7c96.2 docker原生网络host
[root@docker ~]# docker run -it --name test --network host busybox
/ # ifconfig
docker0 Link encap:Ethernet HWaddr 02:42:5F:E2:34:6C
inet addr:172.17.0.1 Bcast:172.17.255.255 Mask:255.255.0.0
inet6 addr: fe80::42:5fff:fee2:346c/64 Scope:Link
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:21264 errors:0 dropped:0 overruns:0 frame:0
TX packets:27359 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:1497364 (1.4 MiB) TX bytes:215202367 (205.2 MiB)
eth0 Link encap:Ethernet HWaddr 00:0C:29:EC:FC:D3
inet addr:172.25.254.100 Bcast:172.25.254.255 Mask:255.255.255.0
inet6 addr: fe80::30b2:327e:b13a:31cf/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:1902507 errors:0 dropped:0 overruns:0 frame:0
TX packets:831640 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:2202443300 (2.0 GiB) TX bytes:849412124 (810.0 MiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:11819 errors:0 dropped:0 overruns:0 frame:0
TX packets:11819 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:1279944 (1.2 MiB) TX bytes:1279944 (1.2 MiB)6.3 docker 原生网络none
[root@docker ~]# docker run -it --name test --rm --network none busybox
/ # ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)6.4 docker的自定义网络
- bridge
- overlay
- macvlan
6.4.1 自定义桥接网络
[root@docker ~]# docker network create my_net1
f2aae5ce8ce43e8d1ca80c2324d38483c2512d9fb17b6ba60d05561d6093f4c4
[root@docker ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
2a93d6859680 bridge bridge local
4d81ddd9ed10 host host local
f2aae5ce8ce4 my_net1 bridge local
8c8c95f16b68 none null local[root@docker ~]# ifconfig
br-f2aae5ce8ce4: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 172.18.0.1 netmask 255.255.0.0 broadcast 172.18.255.255
ether 02:42:70:57:f2:82 txqueuelen 0 (Ethernet)
RX packets 21264 bytes 1497364 (1.4 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 27359 bytes 215202367 (205.2 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
docker0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 172.17.0.1 netmask 255.255.0.0 broadcast 172.17.255.255
inet6 fe80::42:5fff:fee2:346c prefixlen 64 scopeid 0x20<link>
ether 02:42:5f:e2:34:6c txqueuelen 0 (Ethernet)
RX packets 21264 bytes 1497364 (1.4 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 27359 bytes 215202367 (205.2 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0[root@docker ~]# docker network create my_net2 --subnet 192.168.0.0/24 --gateway
192.168.0.100
7e77cd2e44c64ff3121a1f1e0395849453f8d524d24b915672da265615e0e4f9
[root@docker ~]# docker network inspect my_net2
[{"Name": "my_net2","Id": "7e77cd2e44c64ff3121a1f1e0395849453f8d524d24b915672da265615e0e4f9","Created": "2024-08-17T17:05:19.167808342+08:00","Scope": "local","Driver": "bridge","EnableIPv6": false,"IPAM": {"Driver": "default","Options": {},"Config": [{"Subnet": "192.168.0.0/24","Gateway": "192.168.0.100"}]},"Internal": false,"Attachable": false,"Ingress": false,"ConfigFrom": {"Network": ""},"ConfigOnly": false,"Containers": {},"Options": {},"Labels": {}}
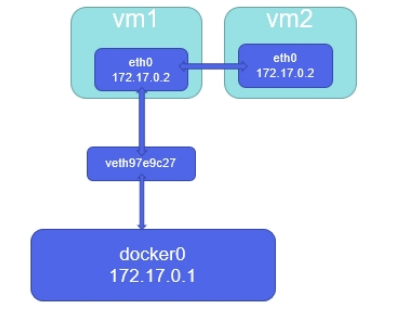
]6.4.2 为什么要自定义桥接
[root@docker ~]# docker inspect web1
"Networks": {
"bridge": {
"IPAMConfig": null,
"Links": null,
"Aliases": null,
"MacAddress": "02:42:ac:11:00:03",
"DriverOpts": null,
"NetworkID":
"2a93d6859680b45eae97e5f6232c3b8e070b1ec3d01852b147d2e1385034bce5",
"EndpointID":
"4d54b12aeb2d857a6e025ee220741cbb3ef1022848d58057b2aab544bd3a4685",
"Gateway": "172.17.0.1",
"IPAddress": "172.17.0.2", #注意ip信息
"IPPrefixLen": 16,
"IPv6Gateway": "",
"GlobalIPv6Address": "",
"GlobalIPv6PrefixLen": 0,
"DNSNames": null
[root@docker ~]# docker inspect web1
"Networks": {
"bridge": {
"IPAMConfig": null,
"Links": null,
"Aliases": null,
"MacAddress": "02:42:ac:11:00:03",
"DriverOpts": null,
"NetworkID":
"2a93d6859680b45eae97e5f6232c3b8e070b1ec3d01852b147d2e1385034bce5",
"EndpointID":
"4d54b12aeb2d857a6e025ee220741cbb3ef1022848d58057b2aab544bd3a4685",
"Gateway": "172.17.0.1",
"IPAddress": "172.17.0.3", #注意ip信息
"IPPrefixLen": 16,
"IPv6Gateway": "",
"GlobalIPv6Address": "",
"GlobalIPv6PrefixLen": 0,
"DNSNames": null
#关闭容器后重启容器,启动顺序调换
[root@docker ~]# docker stop web1 web2
web1
web2
[root@docker ~]# docker start web2
web2
[root@docker ~]# docker start web1
web1
#我们会发容器ip颠倒[root@docker ~]# docker run -d --network my_net1 --name web nginx
d9ed01850f7aae35eb1ca3e2c73ff2f83d13c255d4f68416a39949ebb8ec699f
[root@docker ~]# docker run -it --network my_net1 --name test busybox
/ # ping web
PING web (172.18.0.2): 56 data bytes
64 bytes from 172.18.0.2: seq=0 ttl=64 time=0.197 ms
64 bytes from 172.18.0.2: seq=1 ttl=64 time=0.096 ms
64 bytes from 172.18.0.2: seq=2 ttl=64 time=0.087 ms#在rhel7中使用的是iptables进行网络隔离,在rhel9中使用nftpables
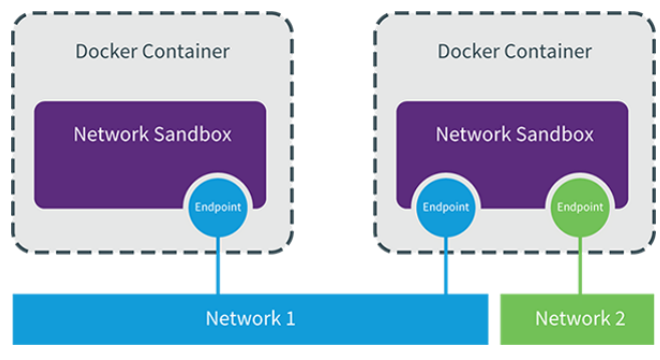
[root@docker ~]# nft list ruleset可以看到网络隔离策略6.4.3 如何让不同的自定义网络互通?
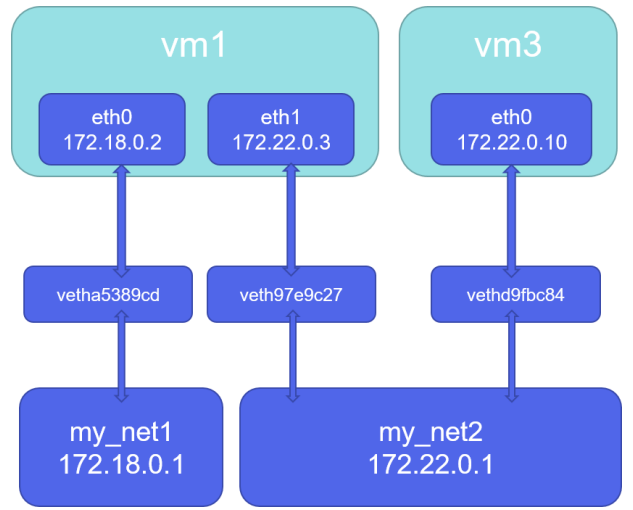
[root@docker ~]# docker run -d --name web1 --network my_net1 nginx
[root@docker ~]# docker run -it --name test --network my_net2 busybox
/ # ifconfig
eth0 Link encap:Ethernet HWaddr 02:42:C0:A8:00:01
inet addr:192.168.0.1 Bcast:192.168.0.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:36 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:5244 (5.1 KiB) TX bytes:0 (0.0 B)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
/ # ping 172.18.0.2
PING 172.18.0.2 (172.18.0.2): 56 data bytes
[root@docker ~]# docker network connect my_net1 test
#在上面test容器中加入网络eth1
/ # ifconfig
eth0 Link encap:Ethernet HWaddr 02:42:C0:A8:00:01
inet addr:192.168.0.1 Bcast:192.168.0.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:45 errors:0 dropped:0 overruns:0 frame:0
TX packets:8 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:5879 (5.7 KiB) TX bytes:602 (602.0 B)
eth1 Link encap:Ethernet HWaddr 02:42:AC:12:00:03
inet addr:172.18.0.3 Bcast:172.18.255.255 Mask:255.255.0.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:15 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:2016 (1.9 KiB) TX bytes:0 (0.0 B)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:4 errors:0 dropped:0 overruns:0 frame:0
TX packets:4 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:212 (212.0 B) TX bytes:212 (212.0 B)6.4.4 joined网络示例演示
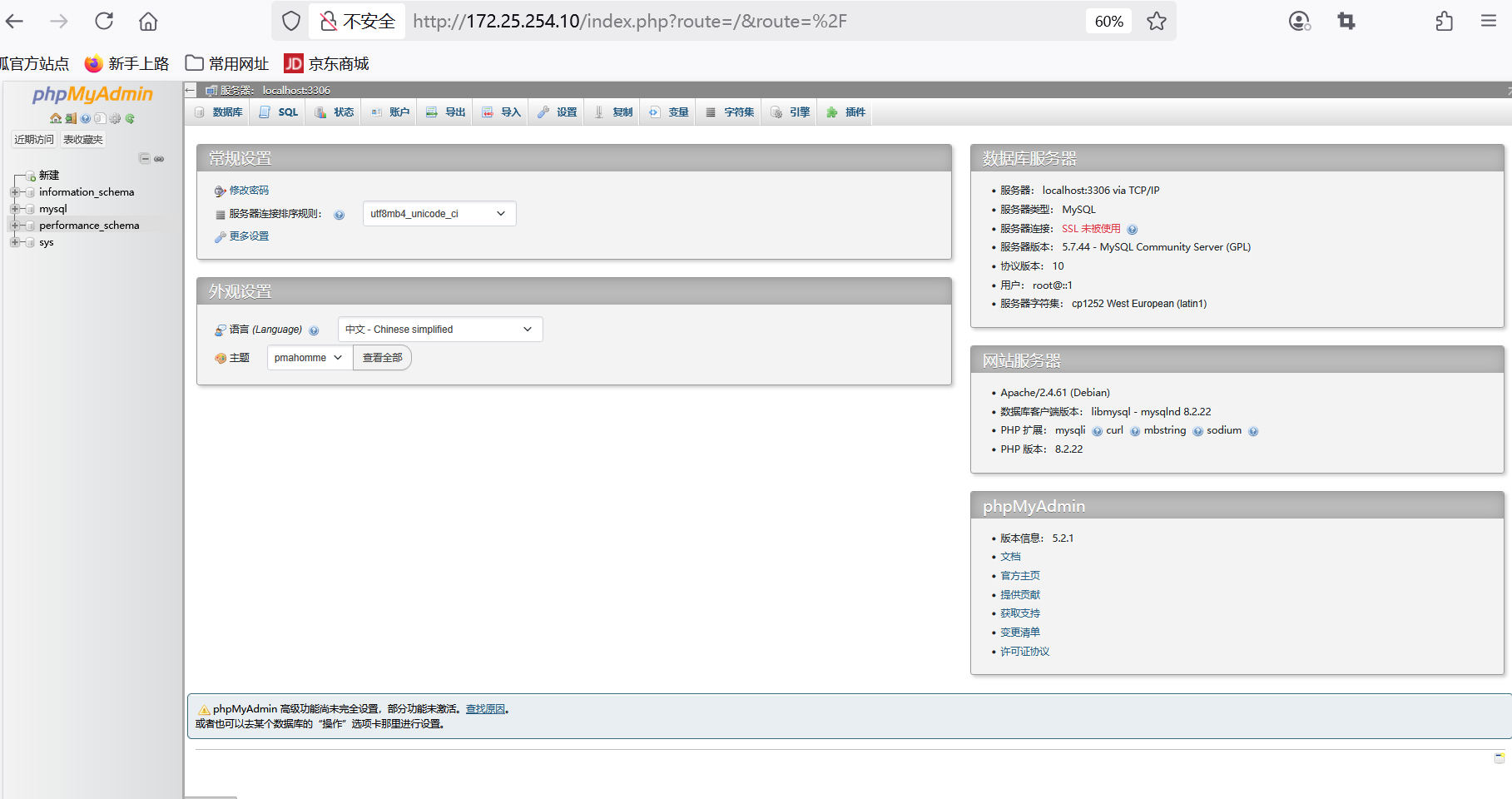
创建名为 my_net1 的网络:
docker network create my_net1将phpmyadmin和mysq镜像进行加载:
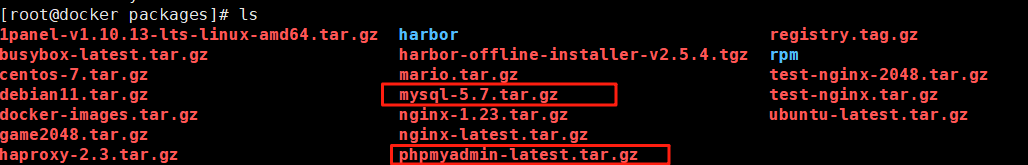
docker load -i phpmyadmin-latest.tar.gz docker load -i mysql-5.7.tar.gz docker run -d --name mysqladmin --network my_net1
-e PMA_ARBITRARY=1 #在web页面中可以手动输入数据库地址和端口
-p 80:80 phpmyadmin:latestdocker run -d --name mysql
-e MYSQL_ROOT_PASSWORD='rin' #设定数据库密码
--network container:mysqladmin #把数据库容器添加到phpmyadmin容器中
mysql:5.7在页面进行访问:

6.5 容器内外网的访问
6.5.1 容器访问外网
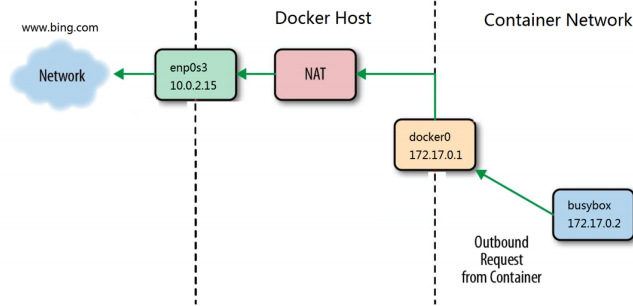
- 在rhel7中,docker访问外网是通过iptables添加地址伪装策略来完成容器网文外网
- 在rhel7之后的版本中通过nftables添加地址伪装来访问外网
[root@docker ~]# iptables -t nat -nL
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
MASQUERADE 6 -- 172.17.0.2 172.17.0.2 tcp dpt:80 #
内网访问外网策略
Chain DOCKER (0 references)
target prot opt source destination
DNAT 6 -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80
to:172.17.0.2:806.5.2 外网访问docker容器
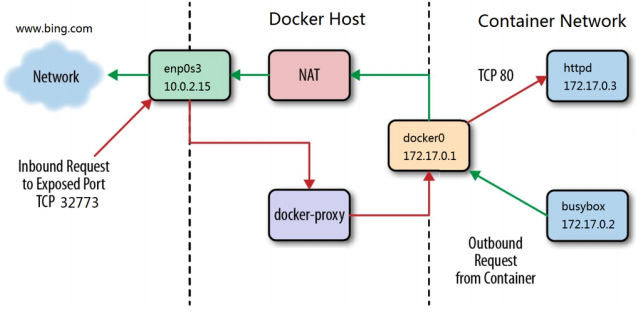
#通过docker-proxy对数据包进行内转
[root@docker ~]# docker run -d --name webserver -p 80:80 nginx
[root@docker ~]# ps ax
133986 ? Sl 0:00 /usr/bin/docker-proxy -proto tcp -host-ip 0.0.0.0 -
host-port 80 -container-ip 172.17.0.2 -container-port 80
133995 ? Sl 0:00 /usr/bin/docker-proxy -proto tcp -host-ip :: -hostport 80 -container-ip 172.17.0.2 -container-port 80
134031 ? Sl 0:00 /usr/bin/containerd-shim-runc-v2 -namespace moby -id
cae79497a01c0b8c488c7597b43de4a43f361f21a398ff423b4504c0905db143 -address
/run/containerd/containerd.sock
134059 ? Ss 0:00 nginx: master process nginx -g daemon off;
134099 ? S 0:00 nginx: worker process
134100 ? S 0:00 nginx: worker process
#通过dnat策略来完成浏览内转
[root@docker ~]# iptables -t nat -nL
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
MASQUERADE 6 -- 172.17.0.2 172.17.0.2 tcp dpt:80
Chain DOCKER (0 references)
target prot opt source destination
DNAT 6 -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80
to:172.17.0.2:806.6 docker跨主机网络
- 跨主机网络解决方案
- docker原生的overlay和macvlan
- 第三方的flannel、weave、calico
- 众多网络方案是如何与docker集成在一起的
- libnetwork docker容器网络库
- CNM (Container Network Model)这个模型对容器网络进行了抽象
6.6.1 CNM (Container Network Model)
6.6.2 macvlan网络方式实现跨主机通信
- Linux kernel提供的一种网卡虚拟化技术。
- 无需Linux bridge,直接使用物理接口,性能极好
- 容器的接口直接与主机网卡连接,无需NAT或端口映射。macvlan会独占主机网卡,但可以使用vlan子接口实现多macvlan网络
- vlan可以将物理二层网络划分为4094个逻辑网络,彼此隔离,vlan id取值为1~4094
- macvlan网络在二层上是隔离的,所以不同macvlan网络的容器是不能通信的
- 可以在三层上通过网关将macvlan网络连通起来
- docker本身不做任何限制,像传统vlan网络那样管理即可
ip link set eth1 promisc on
ip link set up eth1
ifconfig eth1添加macvlan网路
docker network create
-d macvlan
--subnet 1.1.1.0/24
--gateway 1.1.1.1
-o parent=eth1 macvlan1 挂载镜像:
docker load -i busybox-latest.tar.gz 测试:
主机1:
docker run -it --name busybox --network macvlan1 --ip 1.1.1.100 --rm busybox主机2:
docker run -it --name busybox --network macvlan1 --ip 1.1.1.200 --rm busybox[root@docker packages]# docker run -it --name busybox --network macvlan1 --ip 1.1.1.100 --rm busybox
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
13: eth0@if12: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue link/ether 66:6e:ba:48:ba:cc brd ff:ff:ff:ff:ff:ffinet 1.1.1.100/24 brd 1.1.1.255 scope global eth0valid_lft forever preferred_lft forever
/ # ping 1.1.1.200
PING 1.1.1.200 (1.1.1.200): 56 data bytes
64 bytes from 1.1.1.200: seq=0 ttl=64 time=1.086 ms
64 bytes from 1.1.1.200: seq=1 ttl=64 time=0.841 ms
^C
--- 1.1.1.200 ping statistics ---
2 packets transmitted, 2 packets received, 0% packet loss
round-trip min/avg/max = 0.841/0.963/1.086 ms7 Docker 数据卷管理及优化
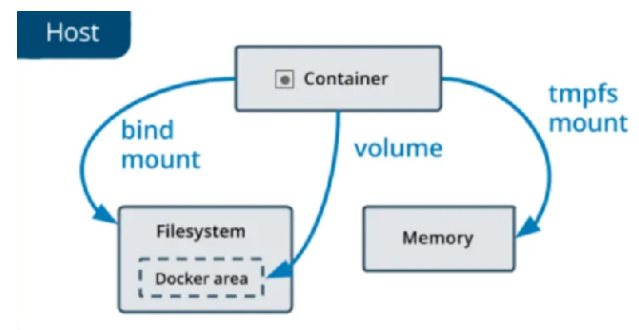
- 数据持久化:即使容器被删除或重新创建,数据卷中的数据仍然存在,不会丢失。
- 数据共享:多个容器可以同时挂载同一个数据卷,实现数据的共享和交互。
- 独立于容器生命周期:数据卷的生命周期独立于容器,不受容器的启动、停止和删除的影响。
7.1 为什么要用数据卷
- 性能差
- 生命周期与容器相同
- mount到主机中,绕开分层文件系统
- 和主机磁盘性能相同,容器删除后依然保留
- 仅限本地磁盘,不能随容器迁移
- bind mount
- docker managed volume
7.2 bind mount 数据卷
- 是将主机上的目录或文件mount到容器里。
- 使用直观高效,易于理解。
- 使用 -v 选项指定路径,格式 :-v选项指定的路径,如果不存在,挂载时会自动创建
在 Docker 中,Bind Mount(绑定挂载) 是一种将宿主机的文件或目录直接挂载到容器内的方式,属于数据持久化的一种手段。它与 Docker 管理的数据卷(Volume)不同,Bind Mount 完全依赖宿主机的文件系统结构,容器直接访问宿主机的指定路径。
Bind Mount 的核心特点
- 直接映射:容器内的路径与宿主机的路径直接绑定,双方的修改会实时同步(无论容器是否运行)。
- 依赖宿主机路径:必须指定宿主机的绝对路径(或相对路径,Docker 会自动转换为绝对路径),若路径不存在,Docker 会自动创建(目录)。
- 权限控制:可通过
:ro(read-only)设置为只读,默认是读写(rw)。- 无命名管理:Docker 不会对 Bind Mount 进行命名或跟踪,完全由用户管理宿主机路径。
创建测试文件:
[root@docker test-2]# echo data1 data1 > data1
[root@docker test-2]# echo data2 data2 > data2[root@docker test-2]# cat data2
data2 data2
[root@docker test-2]# cat data1
data1 data1进行挂载:
docker run -it --rm \-v ./data1:/data1:rw \ # 1. 读写挂载当前目录下的data1到容器内的/data1-v ./data2:/data2:ro \ # 2. 只读挂载当前目录下的data2到容器内的/data2-v /etc/passwd:/data/passwd:ro \ # 3. 只读挂载宿主机的/etc/passwd到容器内的/data/passwdbusybox # 使用的镜像测试:
data1为可读可写,data2为只读
/ # ls
bin data data1 data2 dev etc home lib lib64 proc root sys tmp usr var
/ # cat data1
data1 data1
/ # cat data2
data2 data2
/ # echo docker 1 >> data1
/ # cat data1
data1 data1
docker 1
/ # echo docker 2 >> data2
sh: can't create data2: Read-only file system
/ # cat data2
data2 data2
/ # exit
退出容器后查看本机刚挂载的目录文件情况:
因为文件为挂载文件,所有在容器内部进行更改后,主机的文件也进行了相应的更改
[root@docker test-2]# cat data1
data1 data1
docker 1
[root@docker test-2]# cat data2
data2 data27.3 Docker managed 数据卷
在 Docker 中,Managed Volume(Docker 管理的数据卷) 是由 Docker 引擎自动创建和管理的持久化存储方式,无需用户指定主机上的具体路径,完全由 Docker 负责存储位置的分配和维护。这种方式简化了数据卷的使用,尤其适合需要持久化容器数据但不想手动管理主机文件路径的场景。
Docker Managed Volume 的核心特点
自动创建与管理
- 无需指定主机目录(如
-v /host/path:/container/path),只需在运行容器时指定容器内的挂载点(如-v /data),Docker 会自动在主机的特定目录(通常是/var/lib/docker/volumes/<volume-id>/_data)创建数据卷。- 数据卷的生命周期独立于容器,即使容器被删除,数据卷仍会保留,除非手动删除。
持久化存储
- 容器内写入
/data(假设挂载点为/data)的数据会被持久化到 Docker 管理的主机目录中,避免容器删除后数据丢失。与容器解耦
- 可被多个容器共享和重用,适合多容器协作场景(如数据库容器与应用容器共享数据)
8 Docker的安全加固
[root@docker packages]# free -mtotal used free shared buff/cache available
Mem: 3627 721 2411 9 739 2906
Swap: 4011 0 4011
[root@docker packages]# docker run --rm --memory 200M -it ubuntu:latest
root@e0d90039aafc:/# free -mtotal used free shared buff/cache available
Mem: 3627 756 2377 9 739 2871
Swap: 4011 0 40118.1 解决Docker的默认隔离性
安装lxcfs:
[root@docker rpm]# ls
bridge-utils-1.7.1-3.el9.x86_64.rpm libcgroup-tools-0.41-19.el8.x86_64.rpm lxc-templates-4.0.12-1.el9.x86_64.rpm
docker.tar.gz lxcfs-5.0.4-1.el9.x86_64.rpm
libcgroup-0.41-19.el8.x86_64.rpm lxc-libs-4.0.12-1.el9.x86_64.rpm
dnf install lxcfs-5.0.4-1.el9.x86_64.rpm lxc-libs-4.0.12-1.el9.x86_64.rpm lxc-templates-4.0.12-1.el9.x86_64.rpm -y运行lxcfs并解决容器隔离性
[root@docker rpm]# lxcfs /var/lib/lxcfs &
[root@docker rpm]# docker run -it -m 256m \
-v /var/lib/lxcfs/proc/cpuinfo:/proc/cpuinfo:rw \
-v /var/lib/lxcfs/proc/diskstats:/proc/diskstats:rw \
-v /var/lib/lxcfs/proc/meminfo:/proc/meminfo:rw \
-v /var/lib/lxcfs/proc/stat:/proc/stat:rw \
-v /var/lib/lxcfs/proc/swaps:/proc/swaps:rw \
-v /var/lib/lxcfs/proc/uptime:/proc/uptime:rw \
ubuntu
root@cc08b2ff703b:/# free -mtotal used free shared buff/cache available
Mem: 256 1 254 0 0 254
Swap: 0 0 08.2 容器特权
在容器中默认情况下即使我是容器的超级用户也无法修改某些系统设定,比如网络
[root@docker rpm]# docker run --rm -it busybox
/ # whoami
root
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
2: eth0@if12: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue link/ether 9a:f8:5a:46:af:fd brd ff:ff:ff:ff:ff:ffinet 172.17.0.2/16 brd 172.17.255.255 scope global eth0valid_lft forever preferred_lft forever
/ # ip a a 172.25.254.111/24 dev eth0
ip: RTNETLINK answers: Operation not permitted这是因为容器使用的很多资源都是和系统真实主机公用的,如果允许容器修改这些重要资源,系统的稳定性会变的非常差
但是由于某些需要求,容器需要控制一些默认控制不了的资源,如何解决此问题,这时我们就要设置容器特权
[root@docker rpm]# docker run --rm -it --privileged busybox
/ # whoami
root
/ # ip a a 172.25.254.111/24 dev eth0
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
2: eth0@if14: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue link/ether 7e:d4:04:1d:99:1a brd ff:ff:ff:ff:ff:ffinet 172.17.0.2/16 brd 172.17.255.255 scope global eth0valid_lft forever preferred_lft foreverinet 172.25.254.111/24 scope global eth0valid_lft forever preferred_lft forever#如果添加了--privileged 参数开启容器,容器获得权限近乎于宿主机的root用户
8.3 容器特权的白名单
--privileged=true 的权限非常大,接近于宿主机的权限,为了防止用户的滥用,需要增加限制,只提供给容器必须的权限。此时Docker 提供了权限白名单的机制,使用--cap-add添加必要的权限
capabilities手册地址:capabilities(7) - Linux manual page
#限制容器对网络有root权限
[root@docker rpm]# docker run --rm -it --cap-add NET_ADMIN busybox
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
2: eth0@if16: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue link/ether e2:87:85:ef:35:9e brd ff:ff:ff:ff:ff:ffinet 172.17.0.2/16 brd 172.17.255.255 scope global eth0valid_lft forever preferred_lft forever
/ # ip a a 172.25.254.111/24 dev eth0 #网络可以设定
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
2: eth0@if16: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue link/ether e2:87:85:ef:35:9e brd ff:ff:ff:ff:ff:ffinet 172.17.0.2/16 brd 172.17.255.255 scope global eth0valid_lft forever preferred_lft foreverinet 172.25.254.111/24 scope global eth0 valid_lft forever preferred_lft forever
/ # fdisk -l #无法管理磁盘9 容器编排工具Docker Compose
9.1 Docker Compose 概述
- 使用 YAML 格式的配置文件来定义一组相关的容器服务。每个服务可以指定镜像、端口映射、 环境变量、存储卷等参数。
- 例如,可以在配置文件中定义一个 Web 服务和一个数据库服务,以及它们之间的连接关系。
- 通过一个简单的命令,可以启动或停止整个应用程序所包含的所有容器。这大大简化了多容器 应用的部署和管理过程。
- 例如,使用 docker-compose up 命令可以启动配置文件中定义的所有服务,使用 dockercompose down 命令可以停止并删除这些服务。
- 可以定义容器之间的依赖关系,确保服务按照正确的顺序启动和停止。例如,可以指定数据库 服务必须在 Web 服务之前启动。
- 支持网络配置,使不同服务的容器可以相互通信。可以定义一个自定义的网络,将所有相关的 容器连接到这个网络上。
- 可以在配置文件中定义环境变量,并在容器启动时传递给容器。这使得在不同环境(如开发、 测试和生产环境)中使用不同的配置变得更加容易。
- 例如,可以定义一个数据库连接字符串的环境变量,在不同环境中可以设置不同的值。
- Docker Compose 读取 YAML 配置文件,解析其中定义的服务和参数。
- 根据配置文件中的定义,Docker Compose 调用 Docker 引擎创建相应的容器。它会下载所需 的镜像(如果本地没有),并设置容器的各种参数。
- Docker Compose 监控容器的状态,并在需要时启动、停止、重启容器。
- 它还可以处理容器的故障恢复,例如自动重启失败的容器。
- 服务 (service) 一个应用的容器,实际上可以包括若干运行相同镜像的容器实例
- 项目 (project) 由一组关联的应用容器组成的一个完整业务单元,在 docker-compose.yml 文件中定义
- 容器(container)容器是服务的具体实例,每个服务可以有一个或多个容器。容器是基于服务定义的镜像创建的运行实例
9.2 Docker Compose 的常用命令参数
[root@docker packages]# cat docker-compose.yml
services:web:image: nginx:1.23ports:- "80:80"db:image: mysql:5.7environment:MYSQL_ROOT_PASSWORD: rin以下是一些 Docker Compose 常用命令:
一、服务管理
-
docker-compose up:-
启动配置文件中定义的所有服务。
-
可以使用
-d参数在后台启动服务。 -
可以使用-f 来指定yml文件
-
例如:
docker-compose up -d。
-
9.3 企业示例
利用容器编排完成haproxy和nginx负载均衡架构实施
编辑docker-compose.yml文件:
[root@docker retest]# cat docker-compose.yml
services:web1:image: nginx:latestcontainer_name: web1networks:- mynet1expose:- 80volumes:- /docker/web/html1:/usr/share/nginx/htmlweb2:image: nginx:latestcontainer_name: web2networks:- mynet1expose:- 80volumes:- /docker/web/html2:/usr/share/nginx/htmlhaproxy:image: haproxy:2.3container_name: haproxyrestart: alwaysnetworks:- mynet1- mynet2volumes:- /docker/conf/haproxy/haproxy.cfg:/usr/local/etc/haproxy/haproxy.cfgports:- 80:80networks:mynet1:driver: bridgemynet2:driver: bridge编辑两台web的默认发布命令,文件中将其链接在本机的/docker/web/html1和/docker/web/html2下:
创建默认发布目录文件:
mkdir /docker/web/{html1,html2} -p编写内容:
echo web1 > /docker/web/html1/index.html
echo web2 > /docker/web/html2/index.html编辑haproxy的配置文件,并放到容器与主机链接的目录:
创建配置文件目录:
mkdir /docker/conf/haproxy编辑配置文件:
[root@docker retest]# vim /docker/conf/haproxy/haproxy.cfg
[root@docker retest]# cat /docker/conf/haproxy/haproxy.cfg
globallog 127.0.0.1 local0 infomaxconn 4096daemondefaultslog globalmode httpoption httplogoption dontlognullretries 3timeout connect 5stimeout client 30stimeout server 30stimeout check 5slisten http_load_balancerbind *:80balance roundrobinoption httpchk GET /server web1 web1:80 weight 1 maxconn 200 checkserver web2 web2:80 weight 1 maxconn 200 check
挂载相应的镜像:
[root@docker retest]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
nginx latest 5ef79149e0ec 12 months ago 188MB
haproxy 2.3 7ecd3fda00f4 3 years ago 99.4MB
启动服务栈:
docker compose up -d[root@docker retest]# docker compose up -d
[+] Running 5/5✔ Network retest_mynet1 Created 0.5s ✔ Network retest_mynet2 Created 0.5s ✔ Container web2 Started 1.0s ✔ Container haproxy Started 2.4s ✔ Container web1 Started 1.7s
[root@docker retest]# docker compose ps
NAME IMAGE COMMAND SERVICE CREATED STATUS PORTS
haproxy haproxy:2.3 "docker-entrypoint.s…" haproxy 11 seconds ago Up 11 seconds 0.0.0.0:80->80/tcp, [::]:80->80/tcp
web1 nginx:latest "/docker-entrypoint.…" web1 11 seconds ago Up 11 seconds 80/tcp
web2 nginx:latest "/docker-entrypoint.…" web2 11 seconds ago Up 11 seconds 80/tcp测试:
[root@docker retest]# curl 172.25.254.10
web1
[root@docker retest]# curl 172.25.254.10
web2
[root@docker retest]# curl 172.25.254.10
web1
[root@docker retest]# curl 172.25.254.10
web2